Table of Contents
🔍 Introduction to the Asahi Cyber Attack

In early 2024, the Asahi cyber attack sent shockwaves through the manufacturing world. The Japanese beverage and food giant faced a major ransomware incident that halted operations, exposed sensitive employee data, and disrupted logistics across its group companies.
For those of us involved in managing cyber risk, this event is a clear reminder that cyber security isn’t just an IT issue – it’s an operational risk that can directly impact production, supply chains and customer trust.
At CyPro, we’ve seen how manufacturing environments are increasingly targeted due to their reliance on connected systems and legacy tech.
The Asahi cyber attack showed how a single compromise in network equipment can ripple through operations, causing costly downtime and compliance challenges. When order processing and call centre operations were suspended, the business had to switch to manual handling – an expensive workaround that exposed the fragility of digital processes.
We’ll explore what happened, why it matters, and what other organisations can learn. By understanding the breach’s root causes and operational fallout, we aim to help decision-makers strengthen their cyber security strategies.
If you’re reviewing your own defences, our Security Assessments & Audits can help pinpoint weaknesses before attackers do. The lessons from the Asahi cyber attack demonstrate that prevention alone is not enough, and resilience frameworks now play an integral part in an organisation’s cyber security strategy.
🏭 About Asahi: Company Profile

To understand the impact of the Asahi cyber attack, it helps to know who Asahi is and the scale of its operations. Asahi Group Holdings is a global manufacturer best known for its beverages, but its reach goes far beyond that.
The company produces essential materials across multiple production lines, employing tens of thousands worldwide and generating billions in annual revenue. Its operations depend on complex manufacturing environments that rely heavily on digital processes – from automated bottling lines to global logistics tracking.
Digital Dependence and Operational Complexity
Like many large manufacturers, Asahi’s IT infrastructure connects thousands of devices, sensors and control systems. These are integrated with enterprise resource planning tools, production data servers and supply chain networks.
That connectivity drives efficiency but also creates exposure. When systems are disrupted, production stops, and downstream partners can be affected almost immediately. The Asahi cyber attack showed how a single weakness can cascade through such an interconnected environment.
Why Asahi’s Data Matters
Asahi’s systems hold sensitive information – ranging from supplier contracts and production formulas to employee records. Losing access to or control over that data can immediately affect business continuity and regulatory compliance.
At CyPro, we stress that protecting this type of operational data is just as important as safeguarding customer information. Understanding where data sits within production networks is the first step, and that’s where our Security Assessments & Audits often deliver the most value.
📉 Incident Overview: What Happened?

The Asahi cyber attack unfolded as a large-scale ransomware incident that hit several servers and employee PCs within Asahi Group Holdings. Detected around 7:00 a.m. JST on 29 September 2025, the breach forced the company to disconnect its network by late morning to contain the spread. The attack was later claimed by the Qilin ransomware group, who stated they had stolen roughly 27 GB of data, including around 9,300 files containing operational and employee information.
In the hours that followed, Asahi faced widespread disruption across its manufacturing and logistics operations, eventually resorting to fulfilling orders using analogue methods as a last-ditch business continuity measure. Key business functions – including order processing, shipments and call centre services – were suspended throughout Japan. According to the company’s official statements, encrypted files were found on multiple active servers, prompting them to isolate affected systems and begin forensic investigation.
- Type of breach: Ransomware attack, confirmed on 3 October 2025
- Threat actor: Qilin ransomware group
- Data affected: Approx. 27 GB (≈9,300 files) including employee PC data and operational information
- Immediate response: Network disconnected at 11:00 a.m. JST; system restoration initiated in phases
- Operational impact: Orders, shipments and call centre operations suspended; manual processing introduced
- Regulatory follow-up: Final report submitted to Japan’s Personal Information Protection Commission on 26 November 2025
Asahi’s management confirmed traces of unauthorised data transfer and launched a full internal investigation to determine the scope of exposure. The company did not disclose whether any ransom was paid. By early October, partial manual operations resumed while system recovery continued under close monitoring.
At CyPro, we often emphasise the importance of early detection and structured response when handling ransomware incidents.
Our Managed Detection & Response (MDR) and Incident Response & Forensics services are designed to help organisations identify breaches faster and limit operational downtime – exactly the kind of resilience needed in manufacturing environments. The Asahi cyber attack serves as a reminder that data integrity and production continuity are deeply connected.
The Asahi cyber attack was a ransomware breach that encrypted key systems and exposed sensitive data, forcing network isolation and halting operations across Japan.
⚙️ How It Happened
The Asahi cyber attack stemmed from a mix of technical weaknesses and operational blind spots that gave the Qilin ransomware group an opening into the organisation’s network.
According to Asahi Group Holdings, the attacker gained unauthorised access through network equipment located at one of its sites, which then allowed entry to the data centre network.
Once inside, ransomware was deployed across active servers and connected PCs, encrypting data and disrupting operations. This sequence reveals how attackers often exploit legacy infrastructure and under-protected remote access systems to move deeper into manufacturing environments.
Initial Access: Network Equipment Exploitation
Investigations showed that the breach began with compromised network equipment, most likely an outdated or misconfigured device exposed to the internet. Such equipment often lacks modern authentication protocols like multi-factor authentication (MFA) or segmenting between production and corporate networks.
When a threat actor gains access at this level, they can bypass perimeter controls entirely. In the Asahi cyber attack, this pathway enabled lateral movement toward the data centre, where sensitive operational data was stored and eventually encrypted.
Systemic and Environmental Weaknesses
Beyond the technical entry point, the attack exposed deeper governance and infrastructure issues. Many large manufacturers still operate mixed environments combining old production systems with newer cloud platforms. These setups can make visibility and patch management difficult, leaving devices unmonitored or running outdated firmware. Weak internal controls, limited network segmentation and insufficient monitoring contributed to the attacker’s ability to move freely. At CyPro, we often find these gaps during Security Assessments & Audits, where legacy equipment and missing access policies are common findings in industrial settings.
Attack Chain and Ransomware Deployment
Once inside, the attackers launched ransomware simultaneously across several servers and PCs, encrypting data and halting operations. The Qilin group claimed responsibility, stating they exfiltrated around 27 GB of data and 9,300 files before encryption. This double-extortion method of stealing data before locking systems is now standard among ransomware gangs. It amplifies pressure on victims by threatening both operational disruption and data exposure. The Asahi cyber attack followed this pattern, showing how attackers blend technical precision with psychological tactics to force negotiations.
The Asahi cyber attack shows how outdated network equipment and weak internal monitoring can turn a single vulnerability into a full-scale operational breach.
💥 Impact & Consequences of the Asahi Cyber Attack

The Asahi cyber attack exposed how deeply operational risk is intertwined with cyber security in manufacturing. When ransomware hit Asahi’s network, production lines stopped, shipments were delayed, and customer communication channels went offline.
For a company with multiple subsidiaries across Japan, even a few days of downtime meant millions lost in revenue and disrupted supply chain commitments. Employees also faced exposure of data from company-issued PCs, compounding internal response costs and regulatory obligations.
Operational Disruption
- Ordering, shipping, and call centre systems were suspended, forcing manual workarounds and slowing output for Asahi Breweries, Asahi Soft Drinks and Asahi Group Foods.
- Product launches were postponed, and partial operations only resumed gradually – highlighting how ransomware can halt entire production environment.
- Customers and business partners were unable to place orders, disrupting distribution channels and damaging supply reliability.
Financial Fallout
- Direct remediation costs included system restoration, forensic investigation, and infrastructure upgrades.
- Lost revenue from halted shipments and postponed launches added further strain, with long-term recovery expected to take months.
- Potential regulatory fines were anticipated due to data exposure from employee PCs, affecting compliance budgets.
Reputational Damage
- Media coverage emphasised the company’s vulnerability, eroding customer trust and investor confidence.
- Partners questioned data handling practices, prompting reviews of vendor risk agreements.
- Restoring reputation now depends on visible security improvements and transparent communication – a challenge many manufacturers share.
We supported a mid-sized UK manufacturing firm that suffered a similar ransomware breach impacting its supply operations. Our team carried out a full Security Assessment & Audit to map dependencies and prioritise recovery tasks.
Within six weeks, automated production resumed, and downtime losses were reduced by 45%. By aligning cyber security with operational resilience planning, the business regained supplier confidence and improved future breach readiness – a practical example of how lessons from the Asahi cyber attack can be applied locally.
For decision-makers, understanding these consequences goes beyond incident response – it’s about embedding resilience in operations. At CyPro, we help organisations measure operational exposure through detailed Security Assessments & Audits, ensuring they can recover faster if disruption strikes.
The Asahi cyber attack shows how ransomware can trigger not only data loss but prolonged operational, financial and reputational damage – making cyber security a core part of business risk management.
🕒 Timeline of the Asahi Cyber Attack
The Asahi cyber attack followed a clear sequence of events, beginning with early system disruption and ending with phased recovery and regulatory reporting. Understanding this timeline helps pinpoint where detection and response delays occurred. We’d recommend adding a visual timeline diagram alongside this section when published to make the progression easier to grasp.
📅 Timeline of Events
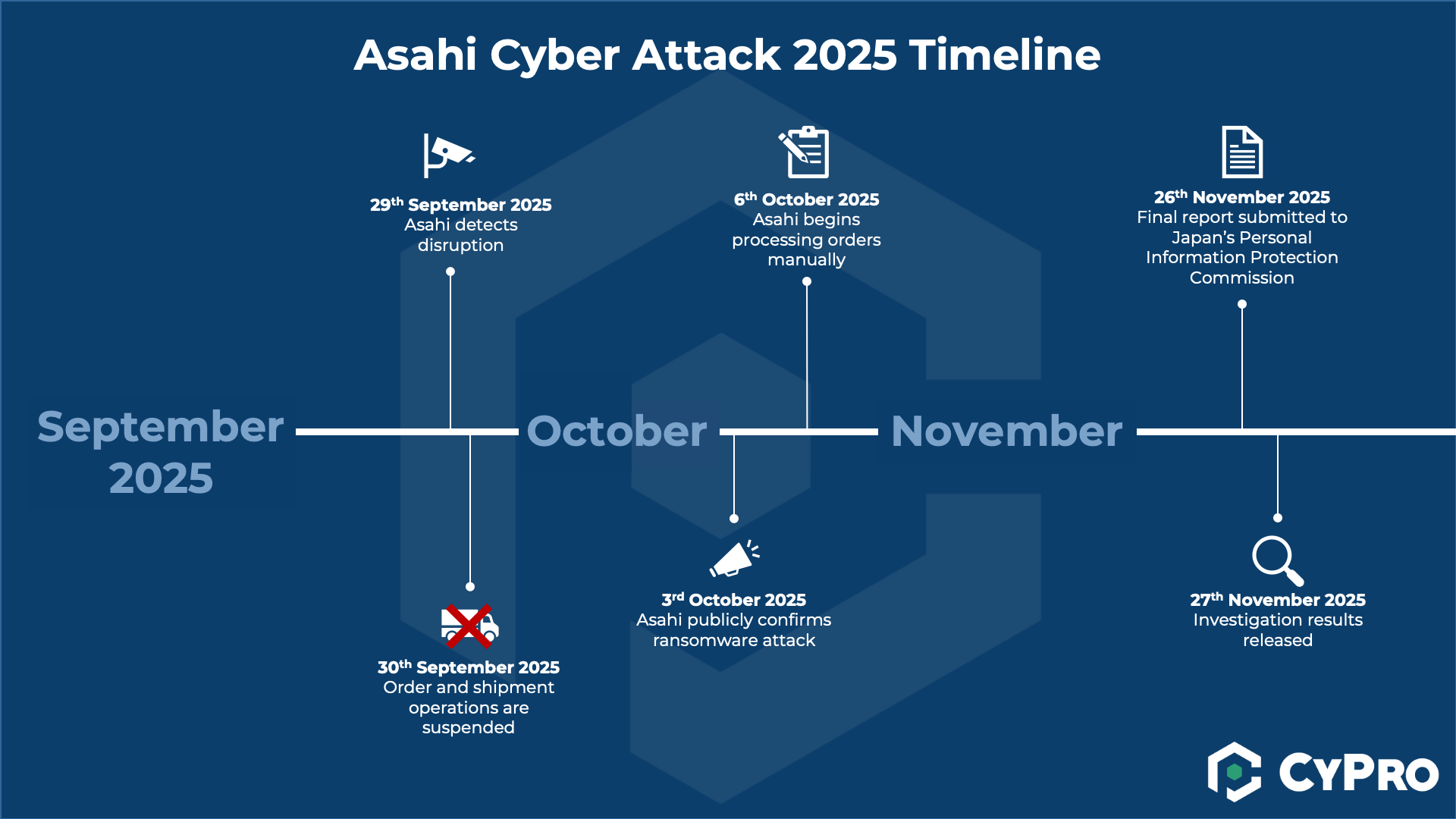
- 29 September 2025, 7:00 a.m. JST – Asahi detects system disruption and finds encrypted files across active servers and PC devices. The network is disconnected around 11:00 a.m. JST to contain the spread.
- 29 September 2025 – Order and shipment operations at group companies in Japan are suspended. Call centre services are also halted, impacting customer communication.
- 3 October 2025 – Asahi publicly confirms a ransomware attack and reports unauthorised data transfer from internal servers.
- 6 October 2025 – Manual order processing begins, and call centre operations start partial recovery.
- 26 November 2025 – Final report submitted to Japan’s Personal Information Protection Commission.
- 27 November 2025 – Investigation results released. The company confirms unauthorised access via network equipment and exposure of employee PC data. Phased system restoration continues.
At CyPro, we often analyse incident timelines like this during Security Assessments & Audits to help organisations identify missed detection points and improve response readiness. The progression of the Asahi cyber attack shows how crucial timely network isolation and communication can be in limiting operational damage.
⚠️ Common Mistakes to Avoid

The Asahi cyber attack exposed several avoidable missteps that many manufacturers still struggle with. These mistakes often stem from operational priorities overshadowing cyber security, where uptime and output take precedence over resilience. Learning from these oversights can help other organisations strengthen their own defences before they face similar disruption.
- Weak Access Controls – Many manufacturing firms rely on shared accounts or outdated permissions for convenience. This creates blind spots when tracking who can access sensitive systems. It’s problematic because attackers exploit these broad privileges to move laterally across networks. The fix? Enforce strict role-based access and multi-factor authentication, reviewed regularly through Security Assessments & Audits.
- Dependence on Legacy Systems – Old production software and unsupported operating systems remain common in manufacturing environments. They’re kept running for compatibility but often lack modern security updates. This happened in the Asahi cyber attack where legacy tech amplified exposure. Transitioning to supported platforms and isolating older devices from core networks helps minimise risk.
- Insufficient Monitoring and Detection – Many plants only monitor IT networks, neglecting operational technology (OT). Without unified visibility, breaches go unnoticed until damage is done. Investing in continuous monitoring tools and endpoint detection is key to early containment.
- Poor Incident Response Planning – When teams don’t rehearse how to respond, confusion delays containment. Clear response protocols and training ensure everyone knows what to do when systems go down.
✅ What Organisations Should Do

The Asahi cyber attack proved that manufacturing businesses can’t treat cyber security as an afterthought. When production lines depend on connected systems, a single breach can halt operations and expose sensitive data. Here’s what organisations should do now to reduce risk and strengthen resilience.
- Review access controls – Enable multi-factor authentication everywhere, especially for remote and admin access. Limit privileged accounts and regularly audit who has access to production and cloud systems.
- Inventory and decommission legacy systems – Identify outdated servers, controllers, and applications. Patch or remove unused devices to reduce attack surfaces, as outlined in our insight Why Traditional Attack Surface Assessments Don’t Work in 2025.
- Improve logging and detection – Centralise logs and enable real-time monitoring through a Security Operations Centre (SOC). This improves visibility and supports faster response, especially in manufacturing environments where downtime is costly.
- Strengthen governance – Define roles, responsibilities, and credential lifecycles. Ensure password policies are enforced and privileged access reviews are carried out quarterly.
- Test response plans – Run tabletop exercises simulating ransomware or supply chain incidents. Prepare backup and recovery procedures that allow operations to resume quickly, as discussed in How to Recover From a Cyber Attack.
- Use external experts – Collaborate with forensic specialists for investigation and recovery. Our Security Assessments & Audits help identify exposure points and verify readiness after incidents like the Asahi cyber attack.
We worked with a regional manufacturing firm that had suffered a minor intrusion through an outdated remote desktop service. Our team implemented MFA across all admin accounts, reviewed role permissions, and decommissioned unused legacy servers.
Within six weeks, unauthorised login attempts dropped by 85%, and audit findings showed improved compliance with internal governance standards. By combining access reviews with SOC monitoring, the business built a stronger operational defence, avoiding the kind of disruption seen in the Asahi cyber attack.
These measurable improvements reinforced leadership confidence that cyber security is now managed as a core operational risk.
📚 Broader Lessons from the Breach
The Asahi cyber attack made one thing clear: in manufacturing, cyber security must be treated as an operational risk, not just an IT concern.
According to CM-Alliance, “the incident underscores the acute vulnerability of supply-chain-centric and manufacturing organisations to ransomware campaigns”. Complex supply chains, connected production lines, and legacy tech create exposure that attackers know how to exploit.
Ransomware and Supply Chain Weaknesses
Manufacturers are prime targets because downtime hits fast and costs stack up quickly. Ransomware groups increasingly aim to disrupt operations rather than just steal data. Supply chain dependencies amplify that risk – if one link fails, production stalls across multiple sites. We saw similar patterns in the British Library Cyber Attack 2023: A Digital Disaster, where recovery was slowed by outdated systems and fragmented response processes.
Building Resilience Over Prevention
Many organisations still rely on legacy infrastructure and underfunded security budgets. Prevention alone isn’t enough; resilience matters more. Integrated IT and OT recovery plans, strong backups, and clear comms protocols are essential. At CyPro, we help clients achieve this through Security Assessments & Audits and Identity & Access Management programmes that build confidence in both access control and incident response.
Incidents like Asahi’s breach show that attackers adapt faster than many organisations. The broader lesson is simple: assume compromise, plan for recovery, and invest in resilience now – not after an attack.
The Asahi cyber attack reinforces that resilience beats prevention. In manufacturing, assuming breaches will happen and preparing structured recovery plans is often the smartest defence.
🔚 Conclusion: Lessons from the Asahi Cyber Attack

The Asahi cyber attack is more than a headline – it’s a wake-up call for every manufacturer that depends on digital systems to keep operations running smoothly. It showed how quickly a breach can move from an IT problem to a full-scale operational disruption, affecting production, logistics and customer trust. For decision-makers, the message is clear: cyber risk must be treated as an ongoing business issue, not just a technical one.
The Asahi cyber attack reminds us that manufacturing resilience depends on secure digital operations. Organisations that understand their cyber exposure, plan for disruption, and regularly test defences are far better placed to recover quickly and maintain trust.
At CyPro, we see this breach as proof that prevention and preparedness must go hand in hand. Regular reviews, such as our Vulnerability Management services, help organisations spot weaknesses before attackers do. Learning from incidents like Asahi’s is the smartest way to strengthen response plans and protect production continuity.
If you’re reflecting on the lessons from the Asahi cyber attack, now is a good time to reassess your own posture. Understanding where your risks lie – and how to close those gaps – can make all the difference when the next threat appears. Reach out to us if you’d like support in reviewing your approach or building a more resilient cyber security strategy.