Insights

How to Build a Security Risk Management Programme in 2026
Security risk management is the process of identifying, analysing and treating cyber risks for a defined business scope. This includes…

Understanding Cybersecurity Standards and Their Real World Implications
Cybersecurity standards are agreed control sets and governance rules that help UK organisations manage cyber risk and evidence good practice.…

What Is Cyber Security? A Plain-English Guide for UK Business Leaders.
Cyber security is the practice of protecting systems, networks and data from unauthorised access, damage and disruption. In the UK,…

How to Implement Automated Incident Response: SOAR, Playbooks and Triggers
Automated incident response links detection to predefined actions so tools can contain threats without waiting for manual approval. It works…

How to Choose a Managed Cyber Security Services Provider
Learn how to select a managed cybersecurity services provider with proven methods for secure operations, compliance and resilience. Start improving…

What a Fully Managed SOC Is and How It Works for Your Organisation
A fully managed SOC is an external team of experts that runs detection, triage and response for your organisation, using…

How to Become a Cyber Security Penetration Tester: A Practical Guide
A cyber security penetration tester simulates authorised attacks on applications, networks and cloud tenants to find and help fix vulnerabilities.…

How to Build a Cyber Security Incident Response Plan for your Business
An incident response plan is the written formal steps that an organisation would take when detecting, containing, and recovering from…

Jaguar Land Rover cyber attack 2025: Post-mortem and Lessons
At CyPro, we analyse the Jaguar Land Rover cyber attack as a 2025 UK incident handled with government and industry…

How to Conduct a Cyber Security Risk Assessment (UK Guide, 2026)
A risk assessment for cyber security identifies and ranks the cyber risks to your organisation and produces a actionable risk…

A Practical Guide to Network Vulnerability Scanning for Organisations
Network vulnerability scanning is an automated process that finds known software and configuration weaknesses across hosts and services and ranks…

What Is Cyber Risk and How UK Boards Should Measure It in 2026
Cyber risk is the likelihood and business impact of objectives being lost or disrupted by cyber incidents, assessed from threats,…

Co-op Cyber Attack 2025: The Hidden Risk of Third-Party Access in Retail
Discover how the Co-op cyber attack exposed third-party access risks in retail and learn 5 vital ways to strengthen security…

Knights of Old Cyber Attack: How a Ransomware Attack Closed a 158-Year-Old Business
Discover how the Knights of Old cyber attack exposed critical ransomware risks and learn 5 vital lessons to protect your…

The Incredible Vercel Data Breach (April 2026): What Happened?
At CyPro, we assess the Vercel Data Breach incident as a suspected third-party breach involving a SaaS integration, with limited…

Expert vCISO Services Explained: What’s Included and When You Need One
At CyPro, we define vCISO services as a contracted senior security leader who provides strategic oversight, governance and risk advice…

Asahi Cyber Attack 2024: Cyber Security as an Operational Risk in Manufacturing
Explore how the Asahi cyber attack exposed operational risks in manufacturing and learn 5 vital steps to strengthen resilience and…

Understanding a Cyber Security Team, Its Structure and Core Functions
A cyber security team is the function that prevents, detects, responds to and recovers from digital incidents across an organisation.…

How Project Glasswing changes vulnerability strategy for UK firms
Project Glasswing matters because public reporting suggests AI-assisted reconnaissance can surface exposed assets faster, while sceptics argue the real impact…

Harrods Cyber Attack 2025: Two Incidents, One Year
Discover how the Harrods cyber attack 2025 was contained through early detection and rapid response, offering vital lessons for retail…

University of Manchester Cyber Attack 2023: When Research Data Became a Target
Explore how the University of Manchester cyber attack exposed research data risks and discover vital lessons for secure academic networks.…

SOC Monitoring Hours Explained: 24/7 vs 12/7 SOC and How to Choose
SOC monitoring hours means the periods when a Security Operations Centre actively watches logs, alerts and telemetry. In the UK,…

An Incredible 30% of UK CISOs Are Buying DSPM (Data Security Posture Management) in 2026
Data Security Posture Management is a continuous way for UK CISOs to discover, classify and prioritise data exposures across cloud,…

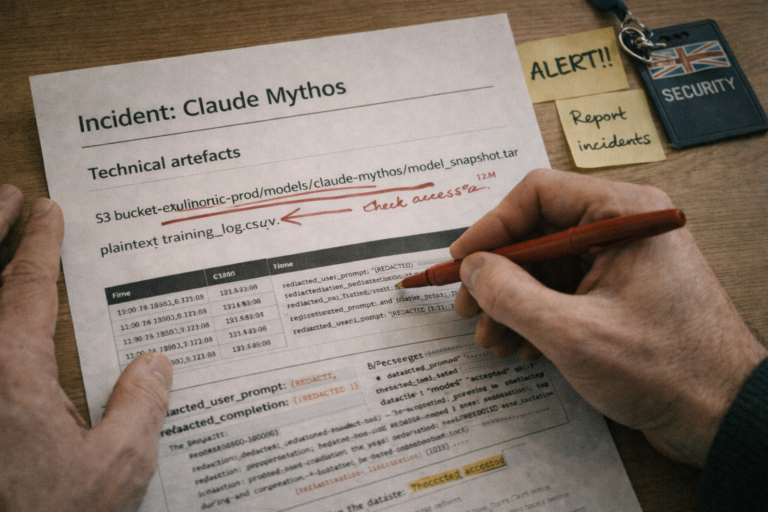
Claude Mythos 2026: Critical Turning Point for Cyber Security or Marketing Hype?
Explore how the Claude Mythos incident reshaped cyber defence in 2026. Learn what it means for AI-driven risk and how…

Modern AI Vulnerability Scanning in 2026: What SMBs Need to Know
SMB security teams should adopt AI vulnerability scanning now as a speed layer, then enforce human validation, ticketed ownership and…

7 Powerful Insights Behind Cyber Security Specialists: Roles, Skills, and Career Paths
Discover what cyber security specialists do, their vital roles, skills and career paths, plus how they protect organisations from digital…

What Does a Virtual CISO Actually Do? Responsibilities Explained
Discover the key virtual CISO responsibilities that strengthen governance, reduce risk and improve compliance for UK organisations. Learn how to…

Cyber Security Audit for Schools: What Headteachers Need to Know
Learn how a cyber security audit for schools protects data, ensures compliance and boosts digital safety. Discover key steps and…

Six Fitness-Inspired Rules for Cyber Security in SMBs
SMBs can build cyber fitness: risk assessment, assess posture, set target state, build resilience, prevent incidents, measure progress. Read how…

Why Cyber Resilience Is More Important Than Cyber Security
Discover why cyber resilience vs cyber security defines business survival. Learn how resilience ensures rapid recovery and lasting trust. Read…

How to Build Cyber Resilience for Your Organisation
Learn how to build cyber resilience with 9 practical steps to protect your organisation, improve recovery and stay secure. Start…

What the Digital Operational Resilience Act (DORA) Means for UK Financial Services
Explore how the digital operational resilience act dora impacts UK financial services, with practical steps to strengthen compliance and resilience.

7 Key Metrics to Measure Your Cyber Resilience
Discover 7 essential cyber resilience metrics that help IT teams measure, improve and prove recovery readiness. Learn how to track…

Managed Security Services Explained: What’s Included and Why It Matters
Discover how a managed security service protects your organisation with 24/7 monitoring, expert response and compliance support. Learn how to…

Virtual CISO vs Full-Time CISO: A Cost-Benefit Analysis
Discover how a virtual CISO compares to a full-time CISO in cost, flexibility and security leadership. Learn which model best…

What Does a Cyber Security Audit Report Look Like?
Discover what a cyber security audit report includes, how it strengthens compliance and protects your organisation. Learn key components and…

SOC vs SIEM: What’s the Difference and How Do They Work Together?
Discover how soc siem integration strengthens detection, response and compliance. Learn 5 essential steps to build a secure, efficient cyber…

How to Conduct a Cyber Security Risk Assessment: Step-by-Step Guide
Learn how to perform a cyber security risk assessment with 7 essential steps to identify threats, reduce exposure and protect…

Cyber Security Roadmap Template: Free Download
Build a powerful cyber security roadmap with our free template. Learn how to prioritise actions, reduce risk, and align strategy…

Cyber Security Audit vs IT Audit: What’s the Difference?
Discover the key differences in cyber security vs IT audit, why both matter for compliance and resilience, and how to…

What Is Cyber Resilience? Definition Principles and Why It Matters
What is cyber resilience? Learn principles to protect operations, recover fast and build trusted business continuity. Read more

The Importance of Cyber Resilience Frameworks And How They Help Your Business
Explore how each cyber resilience framework helps organisations stay secure, meet compliance and recover fast from disruption. Learn which model…

What Does MDR Stand For? Key Terms in Threat Detection Explained
Discover what does MDR stand for and how Managed Detection and Response protects organisations with real-time threat detection and rapid…

What Is MDR? How Managed Detection and Response Works
Discover what is MDR and how Managed Detection and Response improves cyber resilience with expert monitoring and rapid threat action.…

What Does a SOC Team Do?
Discover what a SOC team does, its roles and how it strengthens cyber defence. Learn how to build a secure,…

SOC in Cyber Security: What It Is and Why Your Business Needs One
Discover how a SOC cyber security approach improves detection, compliance and resilience. Learn key components and maturity stages to protect…

What Is a Fractional CISO? A Guide for Growing Businesses
Discover how a fractional CISO strengthens cyber resilience and compliance for growing UK businesses. Learn practical steps to protect and…

Network Security as a Service: Is It Smart for Your Organisation?
Discover how network security as a service helps UK organisations cut risk, boost compliance and stay secure through expert cloud-managed…

What Is a Cyber Audit and When Does Your Business Need One?
Learn how a cyber audit strengthens compliance, reduces risk and builds executive confidence. Discover when your business should act and…

How to Conduct a Cyber Security Assessment: A Step-by-Step Guide
Learn how to conduct a cyber security assessment step-by-step. Discover proven methods to identify risks, improve compliance and protect your…

MDR Meaning in Cyber Security: A Complete Breakdown
Discover the mdr meaning in cyber security and learn how Managed Detection and Response strengthens protection, reduces risk, and builds…

CISO Services Explained: Strategic Security Leadership Without the Overhead
Discover how CISO services provide expert security leadership without full-time cost and how it can strengthen resilience and compliance today.

EDR vs MDR: Which Approach Is Right for Your Business?
Discover how edr vs mdr compares in capability, cost and control. Learn which approach fits your business and strengthen defence…

What Does SOC Mean? A Guide to Security Operations Centres
Discover SOC meaning and learn how a Security Operations Centre protects your business with monitoring, response and compliance. Read our…

Security as a Service (SECaaS): What It Means for UK SMB Businesses
Discover how security as a service helps modern businesses reduce risk, improve compliance and gain reliable protection. Learn practical steps…

CISO as a Service: What It Is and How It Differs from a Full-Time Hire
Discover how CISO as a Service provides flexible, expert cyber leadership and the 5 key ways it differs from a…

What Is Managed Cyber Security? Benefits Models and How It Works
Discover how managed cyber security works, its benefits and models, and how expert services help protect organisations from evolving threats.…

How to Build a Cyber Resilience Strategy for Your Organisation
🔍 Introduction to Cyber Resilience In today’s world, cyber attacks aren’t a question of “if” but “when”. For decision-makers like…

Network Security Monitoring Explained: How It Protects Your Organisation
🔍 Introduction to Network Security Monitoring Network security monitoring is all about knowing what’s happening across your network – not…

Embracing the Essential March 2027 TSA Requirements
🛡️ Why March 2027 Matters The Telecommunications Security Act (TSA) is the UK’s flagship cyber security regime for telecoms. It…

Digital Forensics for SMBs: From Reaction to Readiness
It’s a typical Monday morning. Your small but growing business is back online. Your team logs in, emails fly, invoices…

How Becoming a Pilot Is Changing My Approach to Cyber Security
One morning, I saw an old rugby mate Stuart McInally, had left his post as Captain of Scottish rugby to…

Why Formula 1 and Cyber Security Have More in Common Than You Think
Formula 1 is the ultimate test of engineering, speed and human resilience. Behind every race lies an intricate system of…

Cyber Project Management Is Failing – Here’s How We Rebuild It
Cyber security investment is no longer optional for many small and mid-sized businesses (SMBs). Clients expect it, regulators demand it…

Why Traditional Attack Surface Assessments Don’t Work in 2025
By a UK based cyber security specialist who has spent the last decade translating hacker tactics into board-ready language. 📌…

Is Penetration Testing Dead? Why UK CISOs Are Switching Approaches in 2026
🗝️ Key Points 📉 Why Traditional Penetration Testing is Now a Commodity Traditional penetration testing is not dead, but it…

British Library Cyber Attack 2023: A Digital Disaster
British Library cyber attack 2023 – a devastating ransomware strike that exposed security gaps and crippled a national institution.

The Cyber Resilience Blueprint: Aligning Security with Innovation
🔗 Why True Innovation Depends on Cyber Resilience Innovation without cyber resilience is like building a Formula 1 car without…

How AI Is Advancing 24/7 Cyber Security Monitoring
AI is materially improving 24/7 cyber security monitoring in four specific ways: automating alert triage, correlating signals across SIEM/EDR/cloud, enriching…

What Are Deepfakes & How to Defend Against Them
The rise of artificial intelligence (AI) is a growing concern for organisations. As outlined in our Cyber Awareness for AI…

Should UK Businesses Pay a Ransomware Demand? (2026 Guide)
Short answer: in most cases, UK businesses should not pay a ransomware demand. Paying funds organised crime, risks sanctions breaches under…

What Cyber Security Debt Really Costs SMBs & How to Pay It Down
🧨 Security Debt: The Quiet Liability SMBs Carry Like technical debt, cyber security debt accumulates when small to medium-sized businesses (SMBs)…

A Threat-Led Approach: How to Choose What Your SOC Should Monitor
Welcome to the golden age of log overload. Threat-led 24/7 cyber security monitoring is an approach where Security Operations Centre…

How to Focus on Your Most Pertinent Cyber Security Threats using MITRE ATT&CK
🗣️ Speaking the Same Language in Cyber Security The MITRE ATT&CK framework is a globally recognised, open-source knowledge base of…

A CISO’s Balancing Act: Artificial Intelligence in Cyber Security
🚀 Leveraging AI For Business Growth Artificial Intelligence (AI) is changing the way we operate by automating processes, personalising customer…

Enable Speed to Market via ISO 27001 Certification
Uptake of ISO 27001 certification has increased globally in recent years, and this growth is predicted to continue, as businesses…

Common Pitfalls When Performing a Cyber Security Audit
In an environment where cyber threats evolve as quickly as the technologies designed to stop them, knowing when to run…

The New 2025 Cyber Security and Resilience Bill
Why Did The UK Introduce the Cyber Security and Resilience Bill? The UK Cyber Security and Resilience Bill is new…

Top 10 Free Cyber Security Tools for SMBs
📖 Introduction UK small businesses can build meaningful cyber defences without paying for enterprise software. Free and open-source tools — combined…

How Much Does a Virtual CISO Cost in the UK? (2026 Prices)
Many CxO’s, founders and established IT professionals struggle to get clarity on how much a vCISO service costs and the…

Expert Guide to Technical Due Diligence for Startups
Unlock the secrets of technical due diligence for startups. This guide covers everything from assessing IT infrastructure to ensuring robust…

Cyber Security for SMBs Drives Business Growth
Investing in cyber security for SMBs isn’t just about protection—it’s a growth strategy. For SMBs, robust security measures can open…

Do Small Companies Need a CISO?
In the ever evolving world of digital business where companies need to balance security and customer trust with real-world realities…

The 2021 Telecommunications Security Act (TSA)
The Telecommunications Security Act is a transformative piece of legislation – we discuss how to ensure rapid compliance.

How to Recover From a Cyber Attack
Discover the steps to take that will help you recover from a cyber attack such as ransomware, malware or a…

The Proven Advantage: What Is a Red Team Exercise? A UK CISO’s Expert Guide (2026)
Red team exercises are growing in popularity, but what is a red team exercise, and should you perform one on…

The Importance of Data Privacy Training
With data privacy training, the focus is on your customers and how you gain their trust that you will protect…

Top UK Cyber Security Conferences in 2022
Here’s our rundown of the top UK Cyber Security Conferences in 2022. We hope to see you at one of…

How to obtain the ISO 27001 certification
It’s always nice to add some credentials to your company name. We explain how to obtain the ISO 27001 certification…

When do you need a DPO (Data Protection Officer)?
DPOs can significantly improve your level of compliance with GDPR, but when do you need to a DPO to meet…

What is a vCISO (and should you hire one)?
The adoption of vCISOs is growing in popularity – we explain what is a vCISO and what advantages they bring…

How to Become a Data Protection Officer (DPO)
Many companies are choosing to outsource the role of DPO to skilled consultants – we discuss how to become a…

How to get the Cyber Essentials Certification
Have you heard about Cyber Essentials yet? We explain how to get the Cyber Essentials certification and how this could…

How to become a Virtual CISO (vCISO)
Companies are turning to Vitual CISOs to drive cyber security strategy and implementation. We discuss what it takes to become…

Creating a culture of cyber security at work
Creating a strong culture of cyber security at work adds an additonal and invaluable line of cyber security defence for…

The Importance of Data Privacy for Travel Companies
Travel companies process vast quantities of PII data, putting them at a greater risk of data breaches. We explore the…

Is it time to go paperless to improve security?
Is it time to scrap your print infrastructure and go paperless? It might sound crazy, but only a fifth of…

The real cost of a cybersecurity breach to your business
What would the cost of a cybersecurity breach be to your business? Many businesses struggle to estimate the true impact…

3 reasons why cybersecurity projects fail
The impact of cyber security projects failing is significant, since the organisation will likely remain open to attack. With the…