A cyber security team is the function that prevents, detects, responds to and recovers from digital incidents across an organisation. This covers any event where the confidentiality, integrity or availability of data or systems is compromised. Typically this can range from handling smaller incidents such as phishing (because human involvement remained a dominant factor in breaches in 2025 – Verizon, 2025) through to significant data breaches or platform outages.
The UK Government’s Cyber Security Breaches Survey 2025 shows rising board-level attention to cyber, and the Information Commissioner’s Office publishes data security incident trends, noting over 3,000 notified cyber breaches to the regulator in recent years (ICO, 2025).
- Definition: A cyber security team prevents, detects, responds to and recovers from incidents, combining people, processes and tooling.
- Core functions: Prevention, detection, response and recovery, led by roles such as CISO (Chief Information Security Officer), GRC (Governance, Risk and Compliance) managers, vulnerability managers, SOC analysts, threat hunters and incident responders.
- Common models: In-house, outsourced or hybrid delivery, chosen to match budget, risk appetite and regulations like ISO 27001 and NIS2.
- Daily work: A huge variety ranging across prevention, detection, response and recovery domains. Activities can include implementing new controls like 2FA, performing architectural review, event monitoring, incident triage and response, vulnerability management, and testing resiliency controls like back-ups.
Table of Contents
🔐 What is a cyber security team?
A cyber security team is a group of people responsible for preventing, detecting, responding to and recovering from cyber incidents across an organisation. They combine people, processes and technology to protect data, systems and services from compromise.
Core functions
Prevention, detection, response and recovery are the core functions. Prevention covers policies, identity and access management, patching and security awareness. Detection uses monitoring tools and threat intelligence to spot anomalies. Response contains and eradicates an incident, and recovery restores services and data. The Security Operations Centre (SOC) often runs detection and initial response, while governance and risk live with security leadership and compliance teams.
Organising these functions matters because most breaches still involve human factors: Verizon found that 60 percent of breaches in 2025 involved a human element, such as credential abuse or phishing (Verizon, 2025). In the UK, regular surveying shows board-level attention to cyber risk rising after high-profile incidents and regulatory emphasis (GOV.UK, 2025).
Common team models
Teams usually follow three models:
- In-house
- Outsourced
- Hybrid
In-house teams give tight control and fast internal knowledge. Outsourced models, such as managed monitoring or incident response, scale expertise quickly, provide 24/7 round-the-clock coverage and fill skills gaps; see our 24/7 Cyber Security Monitoring service for example. Hybrid models pair a small internal team with external specialists for surge response or strategic leadership, for example using a Virtual CISO.
What this means for you: Build the functions you need first, then pick a delivery model that matches your risk appetite, budget and regulatory obligations such as ISO 27001, UK GDPR and NIS2. A clear division of responsibilities between IT, security and the board reduces confusion during an incident and speeds recovery.
🛡 How is a cyber security team structured?

A cyber security team monitors for threats, triages alerts, contains incidents and closes the loop with lessons learned, all to reduce business disruption and data loss. A modern team combines people, processes and tooling such as EDR, SIEM and IAM to operates 24×7 where needed.
Day-to-day processes
Monitoring, triage, incident response and vulnerability management are core daily cycles. Monitoring gathers telemetry from endpoints and networks, triage separates false positives from genuine threats, incident response contains and eradicates threats, and vulnerability management reduces the chances of repeat compromises. Most UK security teams prioritise credential protection and phishing defences because human error still features in around 60% of breaches, according to Verizon, 2025.
Tooling and telemetry
Endpoint Detection and Response (EDR), Security Information and Event Management (SIEM), Identity and Access Management (IAM) and Multi-Factor Authentication (MFA) provide the raw signals teams act on. SIEM centralises logs, EDR flags malicious process behaviour, and IAM controls who can access what. Organisations that use automation and security AI tend to detect breaches faster and lower average breach costs, as observed in IBM’s UK analysis IBM, 2025.
Roles and responsibilities
Common roles include a CISO for strategy and board reporting, SOC analysts for monitoring and triage, incident responders for containment, security engineers for controls, and a governance, risk and compliance lead for policy. Clear handoffs between IT, security engineering and business owners speed recovery and limit disruption. Where organisations lack in-house capacity, a Virtual CISO or managed SOC fills gaps.
Frameworks
Frameworks such as MITRE ATT&CK, NIST Cybersecurity Framework (NIST CSF) and the NCSC Cyber Assessment Framework give teams a common playbook for detection, response and improvement. ENISA’s threat environment 2025 highlights why structured threat models matter for prioritising defensive effort ENISA, 2025. In practice, teams align tooling and roles to those frameworks to turn telemetry into repeatable, measurable outcomes.
At CyPro, we help define which of these functions you need in-house and which to outsource, matching controls to regulatory needs such as ISO 27001, UK GDPR and NIS2 so your team focuses on the highest risks.

Team Structure
Typically, there are two types of structure within today’s Cyber Security teams – the Old vs the New.
- The Old (GRC vs SecOPs) – this is where the team or function is split between GRC (governance, risk, and compliance) and SecOps (security operations). This is quite an archaic way of structuring a Cyber Security team and can result in a lot of responsibility cross over, operational confusion and frustration within the team.
- The New (Modular Design) – when structuring a new cyber security team, we recommend a more modular design. This means organising the team around its component parts, aligned to the capabilities it needs to provide, as summarised below.
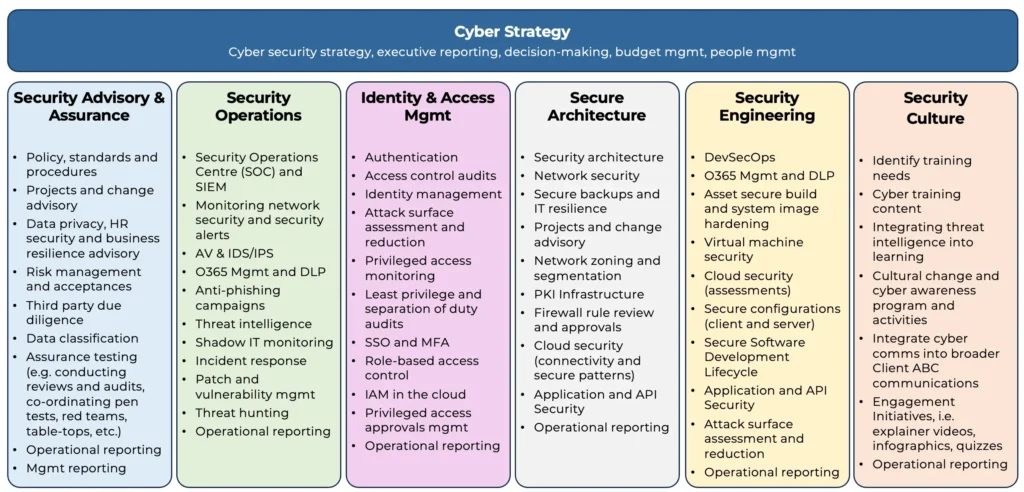
If you want to read up more on how to structure a cyber security team, please use our free Target Operating Model resource below.
🔐 Who needs a cyber security team?
A cyber security team is needed by any UK organisation that handles sensitive data, provides regulated services, or faces material operational disruption from an attack, including financial services, legal firms, technology companies and owners of operational technology.
Regulatory drivers such as UK GDPR, NIS2 and the Financial Conduct Authority (FCA) expectations make having dedicated security capability especially important for regulated firms; large or rapidly growing businesses also reach a point where informal IT-only defences are insufficient.
Size and maturity thresholds
Organisations with more than ~100 employees, multiple cloud workloads, or outsourced IT should consider hiring or outsourcing a cyber security team. The National Cyber Security Centre (NCSC) highlights workforce and capability gaps in its 2025 review, which means many mid-market firms need external support to meet demand (NCSC, 2025). Where headcount or budget is constrained, a Virtual CISO (vCISO) plus a managed service is a common pattern.
Regulatory and sector triggers
Under UK GDPR, organisations that process personal data must implement appropriate technical and organisational measures, which often requires skilled security staff or third-party specialists. The Information Commissioner’s Office (ICO) reports thousands of data security incidents that demonstrate why accountable roles and clear incident plans matter (ICO, 2025).
A UK legal firm, ~180 staff, struggled with slow threat detection and no formal incident playbook. They faced client confidentiality risks and pressure from insurers.
We implemented a vCISO programme and layered 24/7 telemetry with targeted vulnerability scanning, using our Virtual CISO and Cyber Security Audit services to prioritise controls and roles.
Within six months the firm reduced median dwell time by 50% and cut time-to-recovery in tabletop tests by 40%, improving insurer confidence and meeting client contractual requirements.
Choosing whether to hire, build or outsource depends on risk tolerance, regulatory obligations such as NIS2 and DORA where applicable, and the organisation’s ability to retain specialist staff. A focused plan that maps required functions to ISO 27001 controls helps decide which roles to keep in-house and which to buy.
💷 How much does a cyber security team cost in the UK?

A UK in-house cyber security team typically costs between £160,000 and £1.2 million a year depending on size and seniority; managed security options start at £3,000 per month and virtual CISO support from about £20,000 per year.
Decide first which roles you must keep in-house versus what you can buy as a service, then budget for people, tooling and continuous monitoring rather than just headcount.
Cost drivers
Salary and benefits are the largest driver: A mid-level security engineer in the UK costs £55,000-£95,000 per year in 2026, while a senior CISO-level hire will cost considerably more in total compensation.
Tooling and licences for EDR, SIEM, Identity and Access Management (IAM) and vulnerability scanning typically add 20-40 percent on top of salaries. Outsourcing to a managed Security Operations Centre (SOC) replaces some salaries with recurring service fees, but introduces integration and onboarding costs.
Typical models and what they include
Three common models are: In-house, managed SOC, and blended with a virtual CISO. An in-house team suits organisations with bespoke security needs and regulatory obligations such as NIS2 or UK GDPR compliance. A managed SOC gives 24/7 monitoring and incident response for a monthly fee. A virtual CISO supplies senior leadership and strategy without full-time pay.
For industry context, Verizon’s 2025 DBIR notes rising system intrusion rates in EMEA, which affects how much monitoring you need. The same report shows human factors remain dominant in breaches, increasing the value of monitoring and training (Verizon DBIR overview).
| Model | Annual UK cost (2026) | Main inclusions |
|---|---|---|
| Small in-house team (2-4 people) | £160,000-£320,000 | Tactical control implementation, basic tooling, reactive posture |
| Managed SOC | £36,000-£720,000 (£3,000-£60,000 per month) | 24/7 coverage and monitoring, alerting, incident response |
| Virtual CISO + retained Cyber-as-a-Service team | £20,000-£250,000 | Strategic leadership, remediation roadmaps, assurance and audits, part-time governance, proactive posture |
At CyPro, we recommend mapping regulatory duties such as NIS2, UK GDPR and ISO 27001 controls to your chosen model before committing to hires or contracts. If you lack retention capability, consider buying monitoring and a virtual CISO, then hire one or two in-house specialists for platform ownership. Budget for ongoing training and tooling increases, not just the initial hire or onboarding fees.
For practical help, our Cyber Security as a Service page explains blended delivery, and our Cyber Strategy and Roadmap service shows how to convert obligations into a staffed model that matches cost to risk.
🔍 How does a cyber security team differ from managed SOC, MDR and in-house IT?

A cyber security team is an internal group that owns risk decisions, security engineering and incident governance, while a managed Security Operations Centre (SOC) and Managed Detection and Response (MDR) are external or hybrid services that deliver operational detection and response, and in-house IT focuses on availability and user support.
| Dimension | Cyber security team (in-house) | Managed SOC | Managed Detection and Response (MDR) | In-house IT |
|---|---|---|---|---|
| Scope | Strategy, policy, risk decisions, platform ownership | 24/7 monitoring and alerting | Monitoring plus threat hunting and playbooked response | Patching, user support, infrastructure uptime |
| Pricing / TCO | Salaries, training, tooling capital and ops | Monthly retainer, predictable | Per-endpoint or tiered subscription | Existing IT budget, lower marginal cost |
| UK support & compliance | Direct ownership of NIS2, UK GDPR and ISO 27001 duties | UK-based analysts optional, contractual SLAs | Often global teams with UK SLAs available | May lack specialist compliance focus |
| Integrations | Full control of SIEM, IAM and tooling choices | Depends on vendor connectors | Preconfigured sensor and EDR integrations | Limited to operational systems |
| Time-to-value | Months to recruit and mature | Days to weeks to start monitoring | Weeks to deploy sensors and hunting | Immediate for routine ops |
| Organisation fit | Best for regulated, high-risk, or large firms | Good when 24/7 coverage is needed fast | Good when you want hunting without hiring | Fits organisations that prioritise uptime |
Roles and who does what
A cyber security team includes a security leader such as a Chief Information Security Officer (CISO), security architects, threat analysts and a vulnerability manager who set policy and own risk decisions. A managed SOC supplies analysts and shift coverage for monitoring. An MDR provider adds proactive threat hunting and response orchestration. In-house IT focuses on operational tasks such as backups, patching and service desk duties.
Some of the key roles you’d find in the team are outlined below.
- CISO: Sets security strategy and risk appetite, owns overall security posture, reports to board, aligns security with business goals, approves budgets, accountable for incidents and regulatory exposure
- SOC Manager: Runs the SOC function day-to-day, defines processes and SLAs, manages analysts, ensures coverage and tooling works, handles escalations, reports on SOC performance
- SOC Analyst (Tier 1–3): Monitors alerts, triages incidents, investigates suspicious activity, escalates where needed, performs initial containment, documents cases, improves detection through feedback
- Threat Hunter: Proactively searches for hidden threats not caught by alerts, analyses behaviour patterns, develops hypotheses, uses telemetry to uncover advanced attackers, feeds new detections back into SOC
- Incident Responder / DFIR: Leads response to confirmed incidents, performs containment, eradication and recovery, conducts forensics, identifies root cause, supports post-incident reviews
- Vulnerability Manager: Owns vulnerability scanning and prioritisation, manages remediation pipeline, works with IT to patch or mitigate, reports on risk exposure and SLAs, tunes scanning tools
- Penetration Tester: Simulates real-world attacks, identifies exploitable weaknesses, chains vulnerabilities, produces reports with remediation guidance, validates fixes through retesting
- Security Engineer: Builds and maintains security tooling (SIEM, EDR, IAM, etc), implements controls, automates processes, integrates systems, ensures tools are effective and scalable
- Security Architect: Designs secure systems and environments, defines security patterns and standards, reviews designs and projects, ensures security is embedded in architecture decisions
- GRC Manager: Owns governance, risk and compliance, manages policies, risk registers and controls, drives certifications (ISO 27001, SOC 2), liaises with auditors, ensures regulatory alignment
- Compliance Analyst: Maps controls to frameworks, gathers evidence, supports audits, tracks compliance status, maintains documentation
- Identity & Access Management (IAM) Specialist: Manages identities, roles and access controls, enforces least privilege, handles onboarding/offboarding, implements authentication and authorisation systems
- Security Awareness & Training Lead: Runs user training programmes, phishing simulations, drives culture change, reduces human risk
- Third-Party / Supply Chain Risk Manager: Assesses vendor security, manages due diligence, monitors ongoing risk from suppliers, ensures contractual security requirements
- Threat Intelligence Analyst: Collects and analyses threat intel, tracks adversaries, provides context to SOC and hunters, informs detection and defence strategy
When to choose each model
Choose an in-house cyber security team when you must own regulatory duties such as NIS2, UK GDPR or ISO 27001 evidence and want direct control over risk decisions. Choose a managed SOC when you need 24/7 monitoring quickly. Choose MDR when you want hunting and rapid containment without scaling hiring. Choose in-house IT when your primary need is uptime and user support, not threat hunting.
Retain a small internal cyber security team for strategy and compliance, and buy managed SOC or MDR for 24/7 detection and surge capacity when hiring is hard.
At CyPro, we often recommend the hybrid split: Keep platform ownership and governance in a cyber security team and outsource steady-state monitoring to a managed SOC or MDR to fill gaps fast. That combination reduces recruitment pressure while keeping regulatory responsibilities in-house.
For targeted people-focused defence, consider our Cyber Awareness Training to reduce credential and phishing risk. The wider market shows skills pressure is pushing organisations to buy detection services rather than scale teams internally, which affects UK hiring and procurement timelines (Gartner, 2025). Incident recovery is faster when specialised hunting and MDR capabilities are present, supporting the case for outsourcing detection if you cannot retain hunters (Mandiant, 2023).

🧭 When should you build, buy or outsource a cyber security team?
Build when you need long‑term governance, hands‑on platform ownership and tight alignment with business strategy; buy or outsource when you need faster coverage, specialist skills or 24/7 monitoring quickly.
At CyPro, we find three clear triggers that push organisations toward each choice: Regulatory deadlines such as NIS2 or UK GDPR obligations, a recent incident or near miss, and growth events like M&A or cloud migration that expand attack surface. Each trigger changes the tolerance for risk and the speed you need people in post.
When to build: Pros, cons and timeline
Build a permanent cyber security team if you need sustained control over security decisions, bespoke engineering, or to meet long‑term regulatory accountability under NIS2 or the UK GDPR. Building gives you a single accountable team for ISO 27001 or DORA readiness, but it takes time: Hiring, training and embedding usually takes 6-12 months for core capability and 12-24 months for a mature team. Expect higher ongoing costs but better cultural fit and institutional memory.
When to buy or outsource: Faster, more flexible
Buy tools plus services or outsource monitoring when you need speed and specialist skills you cannot hire quickly: 24/7 monitoring, incident response, or short‑term project work. Outsourcing to a managed SOC or an MDR provider delivers time‑to‑value in weeks not months and reduces recruitment pressure. For many UK mid‑market organisations, combining a small in‑house team with outsourced SOC coverage is the fastest route to compliance and operational resilience.
Practical rule of thumb: If you face a regulator deadline within six months, prioritise buying or outsourcing while you build internal capability. If you expect steady growth and repeated security demands over years, plan to build core roles such as a security engineer, an identity lead and a compliance owner.
Advise drafting a 12‑month hybrid roadmap that maps which responsibilities remain in‑house and which are outsourced, then re‑evaluate after one major incident or an organisational change. That keeps accountability clear while you close short‑term gaps with specialist partners such as our Cyber Security as a Service (rel=”nofollow”) and Cyber Strategy and Roadmap (rel=”nofollow”).
Evidence that outsourcing speeds detection: IBM’s breach research shows automation and external detection materially reduce dwell time, improving outcomes in large UK incidents (IBM Report: Cost of a Data Breach, 2025) while Mandiant’s trend analysis shows targeted intrusions remain common and often require specialist response skills (Mandiant M‑Trends, 2023).
🔎 How to choose a cyber security team provider

Choose a provider whose Service Level Agreements (SLA), UK based 24×7 Security Operations Centre (SOC) capability, evidence of well qualified and expert people and a UK support model matching your regulatory exposure and incident tolerance.
Selection criteria you can test
Ask for SLA examples that show detection, containment and recovery targets, and insist on documented incident response playbooks you can read before contracting. The Information Commissioner’s Office (ICO) and the National Cyber Security Centre (NCSC) expect timely breach handling, so suppliers should be able to demonstrate UK incident notification processes and escalation paths.
Request technical evidence: Sample SIEM (Security Information and Event Management) or EDR (Endpoint Detection and Response) dashboards, redacted post-incident reports and SOC runbooks. Check for third-party audit statements such as ISO 27001 certification and penetration test summaries that map to the supplier’s claims.
Questions to ask suppliers and an RFP checklist
Confirm team composition and shifts, your single point of contact, and whether the provider uses a named UK incident manager. Ask about integration with your tooling, data residency and retention, and what role your in-house IT plays during containment. Include priced scenarios in the RFP: A low-severity alert, a ransomware containment and a full disaster recovery exercise.
Validate their detection sources and tuning process, and how they measure mean time to detect and mean time to respond. Remember that human factors still drive many breaches: Verizon’s 2025 report shows a high proportion of incidents involving human elements, so a supplier’s people and playbooks matter as much as tooling (Verizon, 2025).
How to evaluate pricing and contracts
Compare engagement models: Retainer, per-incident, outcome SLA or fully managed 24/7 cover. Ask for total cost examples including onboarding, annual tuning, and major-incident day rates. For UK-regulated firms, ensure the contract supports your reporting obligations and that data flows comply with UK requirements. ENISA’s 2025 analysis highlights rising system-intrusion activity, which increases the value of faster containment and tested playbooks (ENISA, 2025).
Link to a short list: Include a managed option and a consultancy option so you can compare steady-state monitoring against advisory depth. See our Cyber Security Strategy and Roadmap service for structuring a hybrid model and our Virtual CISO service for interim leadership during transition (Cyber Security Strategy and Roadmap, Virtual CISO).
❓ Frequently asked questions
Do I need a dedicated cyber security team if I already have an IT team?
A dedicated cyber security team focuses on prevention, detection and response beyond standard IT operations. In the UK, UK GDPR and NIS2 often make dedicated capability necessary for compliance and reporting. At CyPro, we advise smaller organisations to use managed services or a Virtual Chief Information Security Officer (vCISO), while larger firms usually need in-house security engineers and SOC capability.
How long does it take to stand up a basic security operations capability?
Rapid outsourced monitoring can start in two to eight weeks, while an in-house Security Operations Centre (SOC) commonly takes six to 12 months depending on tooling and hiring. At CyPro, we find timelines depend on log readiness, integrations, recruitment and playbook maturity, and should always include testing and tabletop exercises before declaring the service operational.
Can a Virtual CISO (vCISO) replace a cyber security team?
A Virtual Chief Information Security Officer (vCISO) provides governance, leadership and a roadmap but does not replace hands-on monitoring and incident triage. At CyPro, we use vCISOs to lead smaller teams or oversee managed SOC and MDR arrangements, combining strategic oversight with outsourced or in-house technical capability for full coverage.
What is the typical ROI of investing in a cyber security team?
ROI is commonly measured by reduced incident costs, faster containment and avoided regulatory fines under UK GDPR or NIS2. At CyPro, we recommend quantifying ROI using recent breach cost data and reductions in mean time to detect and contain, then modelling expected savings against the team’s total cost of employment and tooling.
Can a managed SOC or MDR service meet regulatory requirements like NIS2 and UK GDPR?
Managed Security Operations Centre (SOC) or Managed Detection and Response (MDR) services can meet many compliance needs, but legal responsibility under UK GDPR and NIS2 remains with the organisation. Check supplier evidence such as ISO 27001, SOC 2, incident reporting support and clear contractual responsibilities before relying on an external provider for regulatory obligations.
Contact Us












