Table of Contents
📌 Key Takeaways
Claude Mythos raises the question of whether cyber security is truly changing, or simply speeding up trends that were already underway.
Key points to consider:
- Does Claude Mythos represent the start of a major shift in how we work, or simply the next step in an ongoing evolution?
- Is the level of speculation driven more by how Claude Mythos was revealed than by what it can actually do?
- Is Project Glasswing a necessary way to manage risk, or does restricting access to a select group of organisations create an imbalance for others?
- Are the fundamentals (patching, monitoring, and keeping systems up to date) still the most important aspects of cyber security?
- Will the real impact of these technologies emerge gradually through everyday tools, rather than as one defining moment?
🔍 What is Mythos and What Happened?
Developed by Anthropic, who are an artificial intelligence company based in the U.S, Mythos is an unreleased AI model believed to represent a significant advancement in how vulnerabilities in software systems can be identified and understood.
In recent months, Claude Mythos has emerged as a key topic across cyber security and artificial intelligence discussions. It’s been a topic of conversation everywhere; from office desks to LinkedIn to even my dinner table at my parents house, curious about who “Claude” is and why he matters so much to me right now.
Its introduction into the public domain did not follow a traditional launch, but instead came through a series of leaks in March 2026. These included the Claude Code leak, alongside references to Claude Sonnet 5, signalling the next generation of Anthropic’s models.
Anthropic’s disclosures and subsequent commentary from industry groups led to a mix of technical and regulatory scrutiny, with the National Cyber Security Centre (the UK government’s authority on cyber security) highlighting the scale of recent high‑profile incidents in its Annual Review 2025 and the Information Commissioner’s Office (the UK’s independent authority set up to uphold information rights and data protection emphasising AI and data protection) in its Guidance on AI and data protection.
❓What Can Mythos Do, and Why Is It Different?
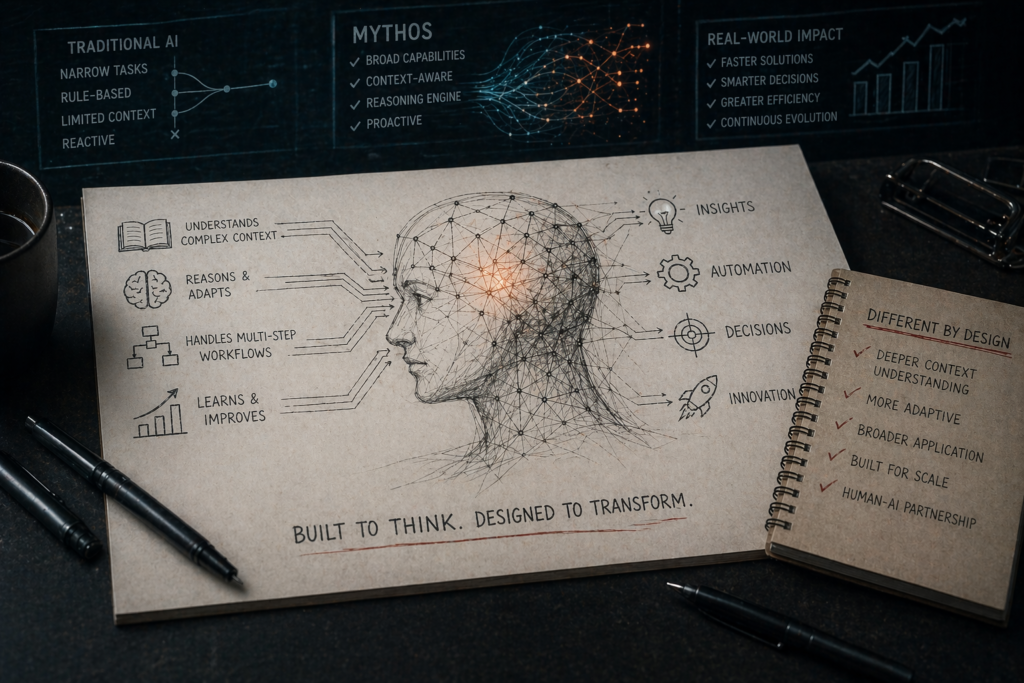
While Mythos shares similarities with existing security tools, its capabilities appear to operate at an entirely different level of sophistication.
Traditional tools typically identify vulnerabilities based on known patterns or signatures. This makes them reliable, and while they require validation, false positives are not frequent.
Mythos, by contrast, is designed to analyse systems holistically: understanding how components interact and identifying weaknesses that may not follow established patterns.
Many zero-day vulnerabilities and other potential lateral movement are usually discovered through non-pattern-based analysis and complex system interactions, which shows huge potential for a complete shift in how we identify vulnerabilities, and how quickly this process can be done.
Reports from the red.anthropic article show that, in controlled environments, Mythos has already identified a significant number of vulnerabilities, including previously unknown zero-day vulnerabilities that have remained undetected for extended periods. Crucially, it is also capable of demonstrating how those vulnerabilities could be exploited, moving beyond detection into simulation.
This represents a shift from AI-assisted security, where tools support human analysts, toward AI-driven processes that can perform multiple stages of the workflow with reduced human input.
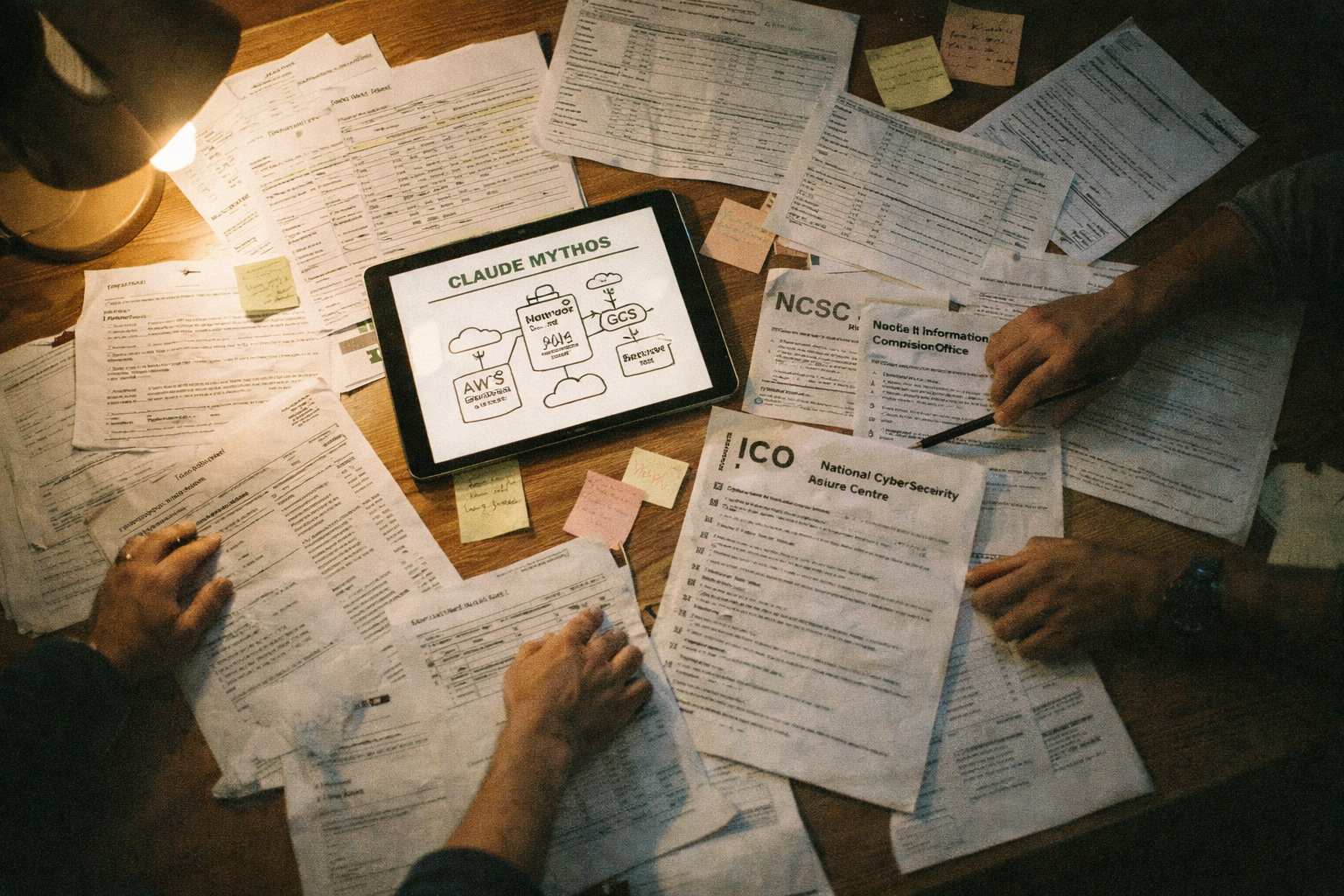
⚙️ What is Project GlassWing?

Given the potential implications, Mythos has not been released publicly.
Instead, it is currently being deployed through Project Glasswing, a controlled initiative involving a limited number of major technology organisations. The objective is to identify and remediate critical vulnerabilities before similar capabilities become widely available.
This approach has prompted discussion around access and fairness. If Claude Mythos really does have the capabilities it has claimed to have, this is a sensible move. Releasing a tool as powerful as this into the wild, and potentially to the hands of those with bad intentions, is dangerous.
The Department of Science, Innovation and Technology have reported that 1 in 2 small businesses have experienced a cyber attack in the past month, and this sort of tooling could increase this number drastically, without leaving room for recovery.
The underlying rationale is grounded in risk management, the volume of vulnerabilities being identified is already challenging the ability of organisations to respond at pace. Restricting access provides a window to address critical issues before broader distribution increases exposure.
However, the argument of ‘gatekeeping’ has come up frequently, and should be explored. Quoted directly from Anthropic themselves on the 7th of April, 2026: “We’re partnering with the organisations responsible for the infrastructure billions of people depend on, and giving their defenders a head start with our newest frontier model, Claude Mythos Preview. The initiative brings together Amazon Web Services, Anthropic, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, the Linux Foundation, Microsoft, NVIDIA, and Palo Alto Networks as launch partners”.
Some would consider this giving a head start to the technology giants, who already have the more advanced capabilities to defend and protect. However, this does fail to consider the bigger picture, that this set up has been done to benefit the community, and not hinder.
⏭️ What We’ve Already Seen vs What Comes Next

AI is already playing a role in cyber attacks. Attackers used AI to support ransomware campaigns, automating tasks such as target identification, code generation, and elements of communication. While these approaches increased efficiency, they remained dependent on human oversight.
Mythos promises a potential evolution of this model. Despite the acknowledgement that all AI conclusions will still be required to be validated by a human, AI could take on a more central role in identifying vulnerabilities, developing exploits, and executing multi-stage attack scenarios.
At the same time, however, this shift has clear defensive applications. The encouragement and convenience of adopting continuous, AI-driven testing models, replacing periodic assessments with ongoing monitoring and validation suggests that the shift will encourage businesses to implement more sophisticated security controls, which is a benefit for the business and supply chain themselves.
This shift points towards a future where cybersecurity becomes more proactive, automated, and continuous.
Is This a Real Shift or a Moment of Hype?
With any emerging technology, it is important to separate underlying capability from the way it is presented.
There is little doubt that Mythos represents a meaningful technical step forward. However, the level of attention it has received is also closely linked to how it entered the public domain and how it has been communicated since. Notably, this follows a similar timeline of events from the OpenAI link of ‘Spud’, discussed by Geeky Gadgets on April 20th, that claims to be able to out-perform competitors, namely Claude Opus 4.7.
Both have conveniently had their capabilities leaked to the public, which naturally raises the question: Is this one of the best marketing ploys we have seen so far, designed to disrupt the cyber community, or are we about to see one of the biggest shifts to autonomous monitoring and detection we have seen?
Particularly from a communications perspective, this is highly effective. It positions the technology as both advanced and scarce, while reinforcing its perceived importance. In many cases, this has the potential to accelerate adoption, investment, and industry focus. However, whilst highlighting these breakthroughs, it also brings about concern.
If processes that have traditionally required human expertise can now be automated, there is a growing question around the impact on roles within cyber security, particularly those focused on manual testing, analysis, and validation.
The extent of speculation is both impressive and concerning, with discussions ranging from widespread job displacement to the complete transformation of security operations into AI-led environments.
It is also worth recognising that organisations developing these technologies operate in a competitive environment. Highlighting breakthroughs, particularly those with significant security implications, can serve both strategic and commercial objectives.
Businesses and organisations value the convenience their AI assistants can offer, and if a competitor can prove to do this more accurately and further in-depth, it is not unreasonable to think they will want to move to the next best thing.
Despite the potential this carries to be a clever marketing strategy in a fast paced environment, at the same time, some caution is warranted. Many of the capabilities described have been demonstrated in controlled settings. Similar patterns have been seen with previous technological advances, where early narratives emphasise potential impact ahead of widespread real-world application.
Therefore, while the smoke and mirrors hypothesis is certainly believable, this and other factors such as the reliability of the businesses involved in Project Glasswing does suggest there may be substance to this.
This does not diminish the significance of the technology, but it does suggest that part of the current response is driven by anticipation, as much as immediate risk.
Will This Actually Change Cyber Security in Practice?
A more practical question for most organisations is whether these developments will materially change cyber security in the near term.
In many respects, no matter whether Claude Mythos does in fact have the capabilities it is suggested it might, the answer is likely to be gradual rather than immediate. However, this also has the potential to slide to either side of the scale, changing very little or entirely the way we work.

Despite the headlines, the core challenges in cyber security remain unchanged. Even if vulnerabilities are discovered more quickly, organisations must still have the processes and capacity to address them.
There are also structural limitations to consider. The discovery of vulnerabilities at scale does not automatically translate into their exploitation. Factors such as access, targeting, and operational complexity continue to play a role in determining real-world impact. Therefore, while mapped in theory, the output of this might significantly differ to what has been portrayed.
From this perspective, Mythos may be better understood as an acceleration of existing trends, rather than a complete transformation.
Where it is likely to have a more visible impact is over the medium term. Even if this is a marketing ploy, similar capabilities are likely to become more widely available, with OpenAI’s ‘Spud’ being an example of such promise. Organisations will likely begin to see:
- Increased volume of vulnerability discovery
- Shorter timeframes between identification and remediation
- Greater reliance on automated security tooling
In this sense, the change is less about a sudden shift and more about a gradual compression of time and effort across the cyber security lifecycle.
Patch Velocity: The New Pressure Point in Cyber Security

However, one of the less visible but increasingly critical implications of tools like Mythos is the impact on patch velocity, or how quickly organisations can respond to and fix vulnerabilities once they are identified.
Historically, vulnerability management has operated on a manageable cycle. Issues are discovered, prioritised, and addressed over days or weeks, depending on severity and available resources. However, if vulnerabilities can be identified at scale and in near real time, the expectations to remediate them may shift. Defined SLAs may no longer be appropriate in this new landscape, meaning a shift in expectations and increased pressure to protect the organisation’s attack surface.
This creates a widening gap between discovery speed and remediation capacity: particularly for organisations without automated processes in place.
In practical terms, this means that the ability to patch quickly is becoming just as important as the ability to detect vulnerabilities in the first place.
There are also broader implications. Faster discovery increases the likelihood that vulnerabilities become known, either publicly or within smaller circles, more quickly. Even if not immediately exploited, the window for response becomes shorter, and the margin for delay reduces.
For many organisations, this will require a rethink of existing processes. Manual patching cycles and periodic updates may no longer be sufficient in environments where vulnerabilities are identified continuously. Instead, there is a growing need for:
- Prioritisation based on real risk, not just volume
- Automation in patch deployment where appropriate
- Closer alignment between security and operational teams
This does not mean that every vulnerability must be addressed instantly. Rather, it highlights the importance of being able to respond at pace where it matters most, when the threat landscape is ever evolving.
This, however, can be considered a positive, as it creates an opportunity. Patching has always been a hot topic, defining how we patch based on where the vulnerability sits, its explotation potential and if they are external facing. In this sense, Project Glasswing has in fact put us at an advantage. It means that we know there is a possibility that a new model could exploit vulnerabilities quicker and in a much more intricate way, giving people time to act now while the model is still in a controlled setting.
Increasing the risk of not meeting defined SLAs could result in a stronger focus on the importance of scanning and remediation, which would be significantly beneficial to a business despite the capabilities Claude Mythos may or may not have.
✔️ What Does This Means For Your Business?
For most organisations, the immediate implication is not the adoption of Mythos itself, but the broader shift it represents.
Cyber security is moving towards a model that is faster, more automated, and increasingly embedded into day-to-day operations. As a result, the window between vulnerability discovery and potential exploitation may continue to narrow.
In practical terms, this reinforces the importance of maintaining strong fundamentals:
- Keeping systems and software up to date
- Ensuring visibility across your IT environment
- Implementing continuous monitoring and response capabilities
- Maintaining core controls such as multi-factor authentication and secure access management
At the same time, organisations should anticipate greater availability of advanced security capabilities. Tools that were once limited to large enterprises are likely to become more accessible, enabling a more proactive approach to risk management.
The focus should be on preparedness rather than reaction, ensuring that your organisation is well-positioned to adapt as these capabilities become more widely adopted.
📍 Conclusion
While Mythos represents a notable step forward, its broader significance lies in what it signals about the direction of travel. The industry is moving towards greater automation, increased reliance on artificial intelligence, and a shift from reactive to continuous security models.
In the short term, this has created opportunity for businesses to address their patch velocity, with the understanding models such as Claude Mythos could become available at any time. In the long term, it signals that we are likely to see a signifiant change in how cyber security professionals operate day to day, and how AI will no longer only be an assistant, but also the main driver.
At the same time, it is important to maintain perspective. The fundamentals of cybersecurity remain unchanged, and the organisations best positioned to navigate this shift will be those that continue to prioritise visibility, control, and responsiveness.
Rather than viewing Mythos as a turning point in isolation, it is more useful to see it as part of a broader transition, one that will unfold over time and shape how organisations approach security in the years ahead.
CyPros AI Readiness Assessment would be the perfect next step to ensure you stay ahead of the curve.
Maybe the real sign things have changed won’t be all the headlines, but when my mum no longer asks who Claude is and is using it in her day-to-day, too.
Is Claude Mythos released?
No, Claude Mythos has not been publicly released. Its capabilities have mainly been discussed following leaks and controlled testing, rather than through an official launch. This means most organisations cannot access or use it directly.
Who has access to Mythos?
Access is currently restricted to a small group of large organisations through initiatives like Project Glasswing. This controlled approach is intended to allow critical vulnerabilities to be identified and addressed before wider release. As a result, most businesses do not yet have direct access.
Is this different from Claude Sonnet 5?
Yes, Mythos appears to go beyond models like Claude Sonnet 5 in terms of reasoning and cybersecurity capabilities. While Sonnet 5 represents a general advancement in AI performance, Mythos is more specifically focused on vulnerability discovery and system-level analysis.
What should my business do?
There’s no need to act on Mythos specifically, but it does highlight the importance of staying up to date with cybersecurity best practices. Focus on keeping systems patched, improving monitoring, and adopting more automated security tools where possible. The goal is to stay prepared as these technologies become more widely available.
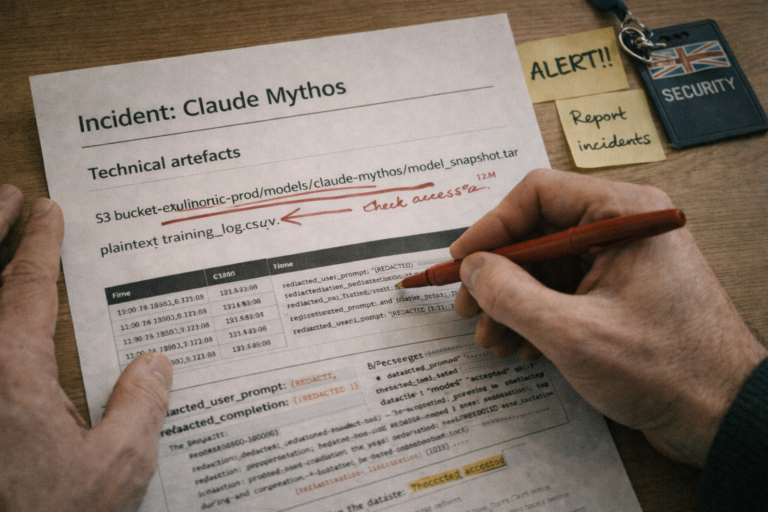
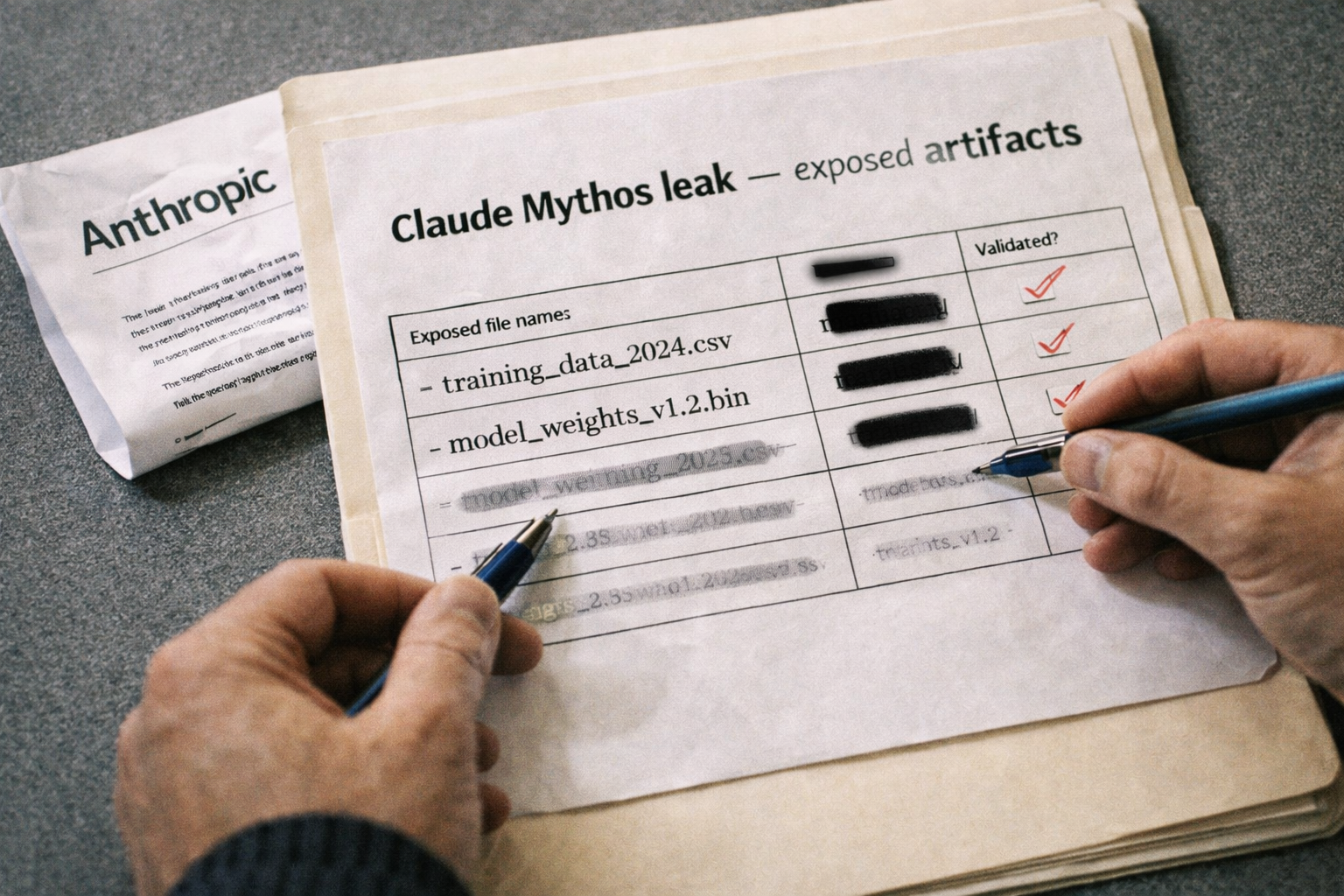
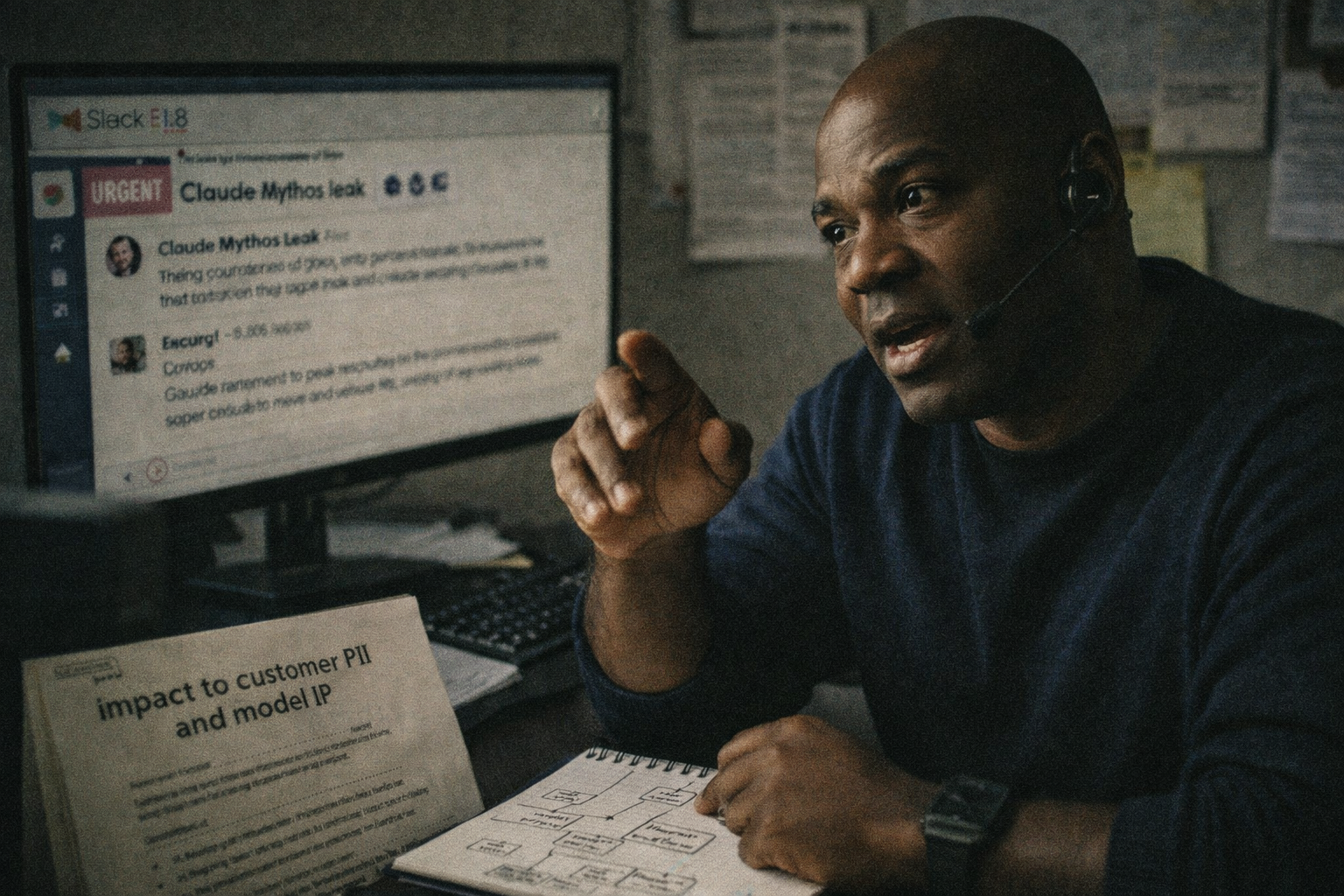
💥 Update: Mythos Hacked?
Reports from the BBC have emerged suggesting that Anthropic are investigating a claim that Claude Mythos may have been accessed by an unauthorised third party, adding another layer of intrigue to an already closely watched development.
If accurate, this raises obvious concerns: particularly around how a system described as tightly controlled under initiatives like Project Glasswing could be exposed, and what the wider implications might be if capabilities like this were to fall into the wrong hands. Given Mythos’ potential to rapidly identify vulnerabilities, even limited external access could, in theory, accelerate how quickly weaknesses are discovered and potentially used.
However, as with much of the Mythos narrative so far, it is worth approaching this with a degree of caution. The timing and nature of these claims invite the question: did this actually happen as described, or is it part of a broader narrative that continues to build momentum around the technology?
Either way, it reinforces the need for strong governance, transparency, and a critical lens when assessing emerging AI developments.