Table of Contents
📜 Introduction to the Digital Operational Resilience Act (DORA)

The digital operational resilience act dora is reshaping how financial institutions in the UK prepare for and respond to technology disruptions. Formally adopted as Regulation (EU) 2022/2554 in December 2022, it enters into application on 17 January 2025, setting new expectations for operational resilience across financial services. As compliance professionals and legal teams know, regulatory shifts like this can have far-reaching implications for governance, risk management, and IT controls.
At CyPro, we work closely with FS organisations to interpret what DORA means for their compliance and governance frameworks. One of our team, Kailey Sharratt, has helped teams align cyber resilience strategies with regulations such as GDPR, ISO 27001 and now the digital operational resilience act dora. In this post, we’ll break down what DORA covers, why it matters, and how UK firms can adapt before enforcement begins. By the end, you’ll understand how the digital operational resilience act dora strengthens operational resilience and what practical steps to take next.
🔍 Overview of the Regulation

The digital operational resilience act dora sets out how financial institutions must manage technology risks and maintain continuity during disruptions. Designed by the European Union, DORA focuses on making sure that banks, insurers, and other FS firms can withstand, respond to, and recover from all types of IT-related incidents. While it’s an EU regulation, UK firms operating across Europe or servicing EU clients will still need to align with its expectations.
Key Themes of the Digital Operational Resilience Act DORA
DORA centres around several recurring themes that mark a shift from pure prevention to resilience:
- Operational Resilience: Firms must prove they can keep crucial services running even when tech fails or cyber events occur.
- Supply Chain Integrity: Third-party providers, especially IT and cloud vendors, are now part of the regulatory picture.
- Incident Reporting: Organisations must report major ICT-related incidents to their competent authorities within strict timelines.
- Governance: Senior management is accountable for resilience policies, testing, and response planning.
We worked with a mid-sized financial services firm that struggled to align its operational resilience framework with emerging EU regulations. Our team conducted a governance review under the principles of the digital operational resilience act dora, identifying gaps in supplier oversight and incident escalation.
Through tailored policy updates and cross-department training, the firm achieved full alignment within six months. They saw a 40% reduction in incident response time and improved confidence from their board in continuity planning.
The result was a streamlined governance model that met DORA expectations and supported broader organisational resilience.
Building Compliance Foundations
At CyPro, we help FS firms embed DORA principles through our Cyber Resilience and Compliance & Governance services. Our consultant Kailey Sharratt works with teams to implement governance structures that align operational resilience with business continuity goals. This includes mapping dependencies, setting clear thresholds for incident reporting, and integrating resilience into board-level oversight.
The digital operational resilience act dora pushes FS firms to think beyond protection and towards sustainability – by embedding resilience, reporting, and governance into everyday operations.
📊 Who Is In Scope
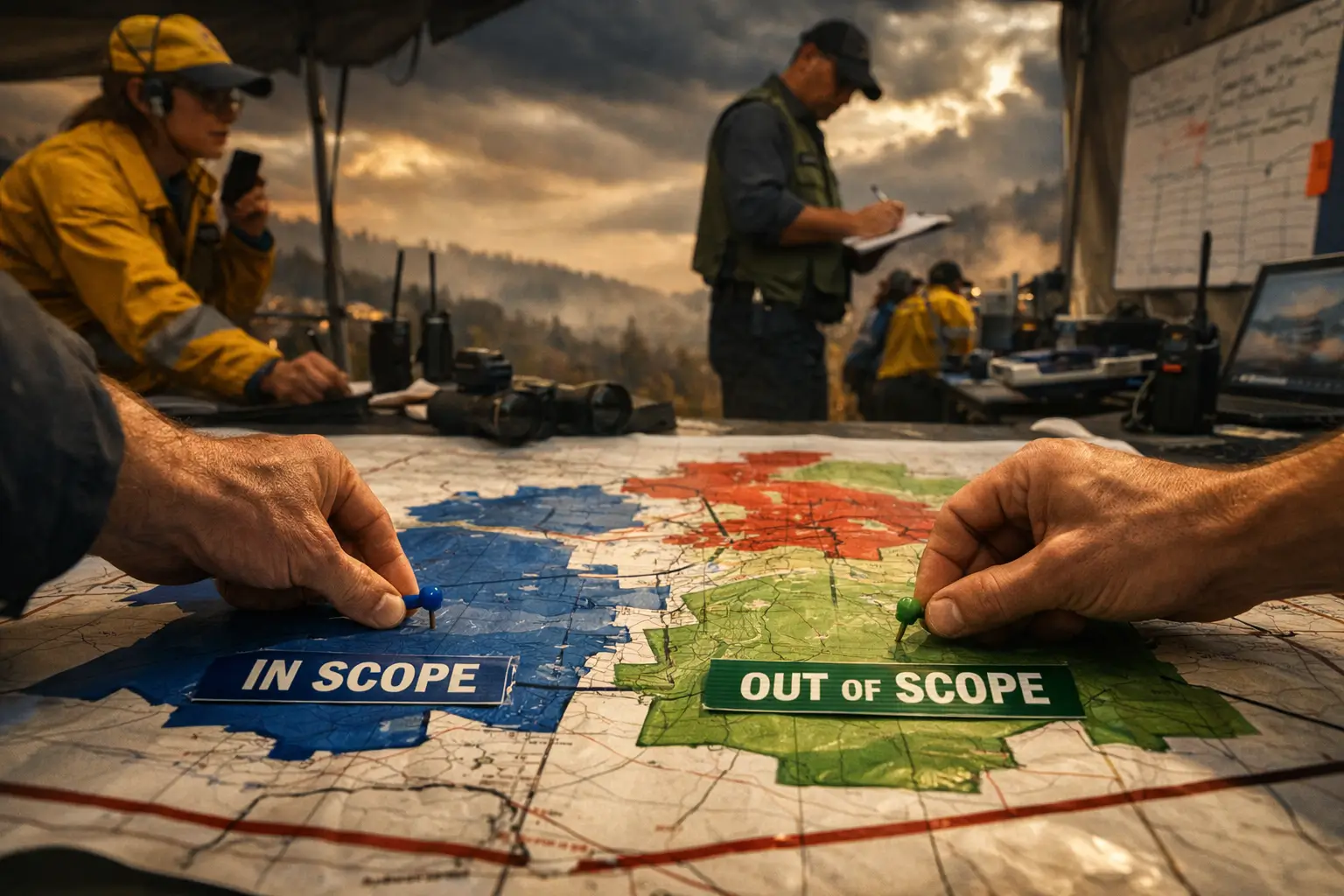
The digital operational resilience act (DORA) applies to a wide range of financial entities and their technology partners.
Whether an organisation is directly regulated, part of a group structure, or a third-party provider supporting FS operations, understanding scope is the first step in preparing for compliance. At CyPro, we help firms analyse their business models, services, and dependencies to determine where they sit under DORA and what obligations follow.
In Scope: Financial Entities and ICT Providers
DORA covers nearly all regulated financial institutions and a growing number of their technology service providers. The regulation recognises that operational resilience extends beyond the financial entity itself to the third parties it relies on. In particular, DORA applies to:
- Banks, credit institutions, and investment firms
- Insurance and reinsurance companies
- Payment and e-money institutions
- Trading venues, clearing houses, and central securities depositories
- Crypto-asset service providers operating in or serving EU clients
- ICT third-party providers deemed crucial to financial operations, such as cloud hosting, data analytics, and managed IT services
Even UK-based firms with no physical EU presence may fall in scope if they provide services to EU customers or partner with EU-regulated institutions. Our Compliance & Governance team often helps FS firms assess these cross-border factors and document their exposure.
We worked with a UK-based payment processor supporting several EU retailers to determine its obligations under the digital operational resilience act dora. The firm was uncertain whether indirect exposure through EU merchants placed it in scope.
Our consultant, Kailey Sharratt, led a review of its client contracts, data flows, and ICT dependencies. We found that its infrastructure supported regulated financial activities within the EU, triggering DORA applicability.
Within three months, we implemented a compliance roadmap covering governance, incident reporting, and vendor oversight. The company achieved full readiness six months before deadline, with a 30% improvement in resilience testing maturity.
Out of Scope: Entities and Activities Excluded from DORA
Not every organisation connected to financial services falls under DORA. Entities that operate outside the EU financial regulatory perimeter or provide purely ancillary services may be out of scope, including:
- Non-regulated firms with no EU presence or clients
- Technology vendors providing general IT support, not financial services infrastructure
- Firms already covered by equivalent national frameworks that do not overlap with DORA’s provisions
However, we often remind clients that being “out of scope” doesn’t mean ignoring resilience. DORA sets a best-practice benchmark that many regulators are expected to align with over time. Building resilience through our Cyber Resilience service can help future-proof compliance and strengthen trust with partners.
The digital operational resilience act dora casts a wide net across FS and ICT providers. Even firms outside direct scope should assess dependencies and align resilience practices to stay ahead of evolving regulatory expectations.
🔑 The 6 Key DORA Requirements

The digital operational resilience act (DORA) introduces a set of structured obligations that reshape how financial services firms handle technology risk and resilience. For compliance professionals and legal teams, it’s more than another checklist – it’s a framework that demands continuous improvement in resilience measures, governance accountability, and incident transparency.
At CyPro, we guide organisations through these requirements, ensuring they not only meet regulatory expectations but also strengthen their operational stability. There are 6 key pillars (requirements) you need to be aware of.
1. Governance and Accountability
DORA places direct responsibility on senior management to oversee resilience strategies. Leaders must ensure that risk management frameworks cover ICT systems, third-party dependencies, and continuity plans. Key governance duties include:
- Embedding resilience objectives within corporate governance structures
- Assigning clear accountability for ICT risk management and reporting
- Ensuring regular board review of resilience testing and response strategies
We often help clients embed these principles through our Cyber Resilience and Compliance & Governance services, aligning resilience with business continuity and regulatory oversight.
2. ICT Risk Management and Testing
Under the digital operational resilience act dora, firms must maintain a robust ICT risk management framework. This includes identifying, assessing, and mitigating risks across all technology functions. Regular resilience testing – both internal and through third parties – is expected to verify that systems can withstand disruptions.
- Conduct annual resilience assessments covering core services and infrastructure
- Implement continuous monitoring of ICT threats and vulnerabilities
- Carry out scenario-based testing to validate response and recovery effectiveness
We supported a mid-sized investment firm with 250 employees in improving its resilience testing under the digital operational resilience act dora. The company had fragmented ICT controls and limited visibility of dependency risks.
Our consultant, Kailey Sharratt, led the implementation of a structured testing programme, including failure simulations and third-party evaluations. Within four months, the firm achieved a 45% improvement in test coverage and reduced response times by 30%.
The outcome was a unified framework that satisfied DORA compliance while enhancing its overall operational resilience posture.
3. Digital Operational Resilience Testing
DORA requires firms to actively prove their resilience, not assume it. Testing must be structured, risk-based and reflective of real-world disruption scenarios.
- Conduct regular resilience testing across systems and services
- Perform scenario-based testing to validate response and recovery effectiveness
- Implement advanced testing, including threat-led penetration testing (TLPT), where applicable
- Continuously improve testing based on outcomes and identified weaknesses
- dent Reporting and Third-Party Oversight
4. ICT Incident Management and Reporting
Timely and structured incident handling is a core requirement. Firms must be able to detect, classify and report incidents in line with regulatory expectations.
- Establish formal incident classification and escalation processes
- Report major ICT incidents to regulators within defined timelines
- Maintain detailed records covering cause, impact and remediation actions
- Ensure post-incident reviews drive improvements in resilience
A common failure point is not detection, but the ability to meet regulatory reporting timelines with accurate data.
5. Third-Party Risk Management
DORA significantly raises expectations around third-party and supply chain risk. Firms are accountable for the resilience of their ICT providers, particularly those supporting critical services.
- Identify and classify critical and important third-party providers
- Implement contractual requirements covering resilience, audit rights and exit strategies
- Continuously monitor third-party performance and risk exposure
- Include key suppliers in testing and incident response scenarios
Concentration risk, particularly around cloud providers, is an increasing area of regulatory focus.
6. Information Sharing
DORA encourages structured collaboration across the financial sector to improve collective resilience.
- Participate in threat intelligence sharing arrangements
- Exchange information on cyber threats, vulnerabilities and incidents
- Use shared intelligence to strengthen internal detection and response capabilities
While often overlooked, this is a practical requirement that supports faster, more informed decision-making.
What this means in practice
DORA is not about adding more controls. It is about proving resilience:
- You understand your systems and dependencies
- You can withstand and recover from disruption
- You control third-party risk effectively
- You can report incidents quickly and accurately
- You continuously test and improve your resilience posture
Most firms underestimate the operational effort required, particularly across third-party oversight and incident reporting. That is where the real work sits.
Our team often helps FS organisations integrate these reporting and supplier management processes through our Cyber Resilience service, ensuring compliance and transparency across ICT environment.
The digital operational resilience act dora demands active governance, thorough ICT risk management, and transparent reporting. Embedding these into daily operations allows FS firms to move beyond compliance and build genuine resilience.
📅 Timeline of Events – Implementing the Digital Operational Resilience Act DORA

The digital operational resilience act dora has a clear and structured rollout, allowing financial services firms to prepare well ahead of enforcement. Understanding key dates helps compliance teams prioritise assessments, resource planning, and governance updates.
At CyPro, we often recommend clients visualise the timeline as part of their project plan – a simple diagram or Gantt-style chart can make milestones easier to track.

Chronological Overview
- 14 December 2022 – Formal Adoption: The Regulation (EU) 2022/2554 was officially adopted by the European Parliament and Council. This marked the formal birth of the digital operational resilience act dora, setting the foundation for harmonised operational resilience standards across all EU financial entities.
- Early 2023 – Initial Guidance and Preparations: EU authorities began releasing clarification notes and working documents to help firms interpret regulatory language. Many UK-based FS organisations started mapping existing resilience frameworks against DORA’s requirements, often with support from consultants like Kailey Sharratt within our Compliance & Governance team.
- Throughout 2023–2024 – Implementation Phase: Financial institutions have been expected to review ICT risk management frameworks, update governance structures, and test incident response capabilities. At CyPro, we’ve seen many clients use this period to align internal policies and conduct readiness assessments before enforcement.
- 17 January 2025 – Regulation Enters Application: According to EIOPA, DORA officially applies across the EU on this date. Firms must be compliant by this point, with fully operational ICT risk management, testing, and third-party oversight processes. UK organisations servicing EU clients will need to demonstrate conformity with DORA’s resilience standards from this day forward.
- 2025 and Beyond – Ongoing Enforcement and Refinement: Supervisory authorities will begin enforcing compliance. Regular reviews, incident reporting, and resilience testing cycles will become part of business as usual. At CyPro, we help clients embed these routines through continuous improvement and governance tracking.
For project managers and compliance officers, these milestones outline a steady path from policy formation to active compliance. A visual timeline diagram here could reinforce how each period builds on the previous one – from adoption to full implementation.
The digital operational resilience act dora follows a structured timeline – adopted in December 2022, enforced from January 2025 – giving firms a clear window to align governance and resilience frameworks. We help FS organisations use that time effectively to achieve compliance readiness before enforcement begins.
⚖️ Comparison with Common Frameworks

The digital operational resilience act dora overlaps with several frameworks already familiar to compliance teams, such as ISO 27001, NIST CSF and GDPR. Each shares a common goal – building trust through robust risk management – but DORA’s focus is broader, placing operational continuity and third-party oversight at the centre. At CyPro, we often help FS firms map their existing controls against DORA’s expectations to identify where enhancements are needed rather than starting from scratch.
Aligning DORA with ISO 27001 and NIST CSF
ISO 27001 provides a structured approach to managing information security, while the NIST cyber security Framework (CSF) focuses on identifying, protecting, detecting, responding and recovering from incidents. The digital operational resilience act dora builds on these by demanding continuous resilience testing, board accountability and reporting of ICT incidents to authorities. In practice, organisations with mature ISMS or NIST-aligned controls already have a head start, though DORA requires a stronger focus on operational impact analysis and third-party dependency mapping.
How DORA Differs from GDPR
Although both regulations share compliance principles, GDPR deals with data protection, whereas DORA addresses service continuity. A data breach under GDPR might involve personal information loss; under DORA, the concern extends to how that breach affects crucial financial operations. Our Compliance & Governance service helps firms align these obligations efficiently, ensuring consistent reporting and governance structures across both regimes.
We supported a mid-sized investment firm already certified to ISO 27001 that wanted to prepare for compliance with the digital operational resilience act dora. We reviewed its ISMS controls and found that 70% already aligned with DORA’s governance, testing and incident response requirements.
We introduced new resilience testing processes and integrated vendor oversight into their risk register. Within four months, the firm achieved measurable improvements in continuity planning and reduced audit preparation time by 35%.
This approach transformed existing compliance work into a foundation for full DORA readiness.
Our team at CyPro often combines Cyber Resilience and Compliance & Governance expertise to help clients integrate DORA into their broader frameworks. This ensures that resilience isn’t treated as a separate project but as part of everyday governance and operational practice.
Firms already aligned with ISO 27001, NIST or GDPR can leverage those foundations to meet DORA requirements. The digital operational resilience act dora simply extends existing best practice by demanding proof that operations can withstand real-world disruption.
💥 Impact & Consequences of the Digital Operational Resilience Act DORA

The digital operational resilience act dora introduces wide-reaching operational, financial, and reputational consequences for UK financial services firms working with EU clients.
Operationally, it demands that banks, insurers, and payment institutions prove their ability to withstand and recover from ICT disruptions. This includes mandatory resilience testing for crucial third-party providers such as cloud platforms and analytics services, as outlined by digital-operational-resilience-act.com. For many organisations, this means new oversight processes and stricter service level agreements with vendors to meet compliance thresholds.
Financially, non-compliance can result in enforcement penalties and increased audit exposure. Firms that fail to meet resilience standards risk suspension of cross-border operations or loss of EU contracts. The upfront cost of compliance – particularly for ICT risk management and testing – can be substantial, but the long-term savings from avoiding downtime and reputational damage often outweighs these initial investments. Our consultant Kailey Sharratt often reminds clients that building resilience isn’t just about meeting DORA obligations; it’s about safeguarding commercial continuity. We support this through our Cyber Resilience and Compliance & Governance services, helping firms design frameworks that protect operations and profitability.
Reputationally, the consequences can be lasting. Under DORA, incident transparency and regulatory reporting will make resilience performance more visible. A firm that handles disruption well may gain trust from clients and regulators, while one that fails publicly could face long-term brand damage. For UK FS organisations working in EU markets, this visibility raises the stakes for maintaining dependable operations and strong vendor oversight.
We worked with a UK-based investment platform serving EU clients that struggled with fragmented ICT incident management. When the digital operational resilience act dora came into view, the business faced risks of non-compliance and potential client loss.
Our team mapped its ICT dependencies and implemented a unified resilience framework combining business continuity and IT Disaster Recovery processes. Within nine months, the firm reduced incident recovery time by 45% and achieved full compliance readiness.
Beyond regulatory alignment, the company gained new investor confidence and secured two EU contracts that had previously been at risk.
In the longer term, DORA will standardise resilience expectations across the FS sector, meaning firms slow to adapt could find themselves commercially disadvantaged. As oversight extends to ICT providers, supply chain resilience becomes a shared responsibility – those with robust controls will stand out as preferred partners. At CyPro, we help organisations prepare for this shift by embedding resilience testing, vendor risk assessments, and governance structures that reflect DORA’s focus on continuous improvement.
The digital operational resilience act dora reshapes resilience expectations for UK FS firms – those investing early in operational, financial, and reputational safeguards will not only meet compliance demands but gain lasting competitive advantage.
⚠️ Common Mistakes to Avoid with the Digital Operational Resilience Act (DORA)

Implementing the digital operational resilience act dora can feel daunting, especially for UK FS firms juggling multiple regulatory obligations. We often see the same pitfalls crop up during early compliance planning. Understanding them helps minimise delays and wasted effort.
- Misinterpreting Scope: Many firms assume DORA only applies to large EU-based institutions. In reality, cross-border services or partnerships often trigger obligations. This happens because supply chains blur regulatory boundaries. The fix? Conduct a thorough scope assessment early, ideally alongside our Cyber Resilience team and Compliance & Governance specialists.
- Underestimating Technical Effort: Some organisations treat DORA compliance as a paperwork exercise. In truth, resilience testing and ICT risk management demand real technical upgrades. Ignoring this leads to rushed implementations and poor documentation. Align tech teams and compliance leads from day one.
- Neglecting Third-Party Dependencies: Overlooking cloud or managed service providers can leave major compliance gaps. DORA explicitly includes ICT partners, so failing to map dependencies undermines resilience.
The digital operational resilience act dora isn’t just another compliance checklist – it’s about building lasting resilience. Getting scope, technical readiness and supplier oversight right from the start saves money and stress later.
✅ What Organisations Should Do to Meet the Digital Operational Resilience Act DORA

The digital operational resilience act (DORA) expects FS organisations to prove they can withstand and recover from technology disruptions. At CyPro, we think the simplest way to start is by focusing on practical, high-impact actions. Here’s what organisations should do next to align with DORA and strengthen resilience.
- Review access controls – Enable multi-factor authentication (MFA) for all accounts, especially remote and admin access. Check privilege levels regularly and revoke unused credentials.
- Audit legacy systems – Inventory every application and server. Decommission anything unused, and set a clear patch management routine for what remains.
- Enhance monitoring – Improve logging and detection capabilities. A well-run SOC helps identify issues early and supports incident reporting under DORA.
- Define governance – Assign clear roles and responsibilities for resilience, including credential management and lifecycle reviews. Our Cyber Resilience and Compliance & Governance services can help build these frameworks effectively.
- Test response readiness – Run tabletop exercises simulating cyber incidents and system outages. Confirm that backup and recovery plans actually work under pressure.
- Seek independent validation – External audits, penetration tests, and security maturity assessments can highlight blind spots and reassure regulators.
We partnered with a mid-sized insurance provider that wanted to prepare for compliance under the digital operational resilience act dora. Their systems were fragmented, and incident response was largely reactive.
Our consultant, Kailey Sharratt, led a full resilience review covering governance, monitoring, and recovery testing. Within four months, the firm consolidated its access controls, retired six legacy servers, and introduced MFA across all core systems.
Post-project, their incident detection time improved by 45%, and recovery testing success rose to 92%. The business now demonstrates measurable operational resilience aligned with DORA’s expectations.
🎯 Your Next Steps for DORA Compliance

The digital operational resilience act dora marks a major shift for UK financial services, pushing firms to build resilience into their technology and governance models rather than relying solely on protection. It’s not just about compliance – it’s about futureproofing operations against disruption and strengthening trust with customers and regulators alike. Getting ahead of DORA’s requirements now will make the transition smoother and minimise regulatory risk later.
DORA demands proactive resilience, structured governance and robust testing. Early preparation helps FS organisations avoid penalties, maintain continuity and build stronger confidence in their digital operations.
At CyPro, we help firms translate the digital operational resilience act dora into practical action through our Cyber Resilience and Compliance & Governance services.
Our specialist Kailey Sharratt works with FS teams to design resilience frameworks that meet regulatory expectations and enhance operational readiness.
Now is the time to review your posture and identify gaps before enforcement begins – reach out to us to start building resilience that lasts.










