Table of Contents
🔍 Introduction to the Knights of Old Cyber Attack

The Knights of Old cyber attack stands as one of the most sobering examples of how ransomware can devastate even well-established businesses. In mid-2023, the 158-year-old UK logistics firm Knights of Old, part of KNP Logistics, was hit by the Akira ransomware group. Within weeks, operations ground to a halt, staff were locked out of systems, and by September, the business had ceased trading entirely – leaving more than 700 people without jobs.
For organisations that rely heavily on IT systems for daily operations, this incident is a clear demonstration of how one breach can spiral into total shutdown. The Knights of Old cyber attack isn’t just a cautionary tale about ransomware, it’s a reminder that recovery plans, detection capabilities and resilience strategies need to be more than just tick-box exercises.
In this article, we’ll unpack what happened, how the attackers gained access, and what lessons other organisations can draw from the event. At CyPro, we help firms strengthen their cyber resilience through practical defence measures like Managed Detection & Response (MDR), giving teams early visibility of threats and time to act before damage is done. By the end, you’ll have a clearer picture of why learning from the Knights of Old cyber attack can be crucial to protecting your own business.
Why Knights of Old Was a Prime Target
- Data sensitivity: Logistics firms handle large volumes of client data, shipment details and financial records – valuable to attackers for extortion and resale.
- Operational dependence on IT: Automated scheduling and real-time tracking meant downtime equalled immediate loss of service.
- Complex supply chain links: Third-party connectivity often introduces hidden vulnerabilities that can be exploited.
These factors made the Knights of Old cyber attack particularly damaging, as ransomware disrupted not just internal systems but partner operations too. It highlights how legacy businesses that have modernised digitally often face risks tied to older infrastructure or incomplete security upgrades.
| Number of Staff | ~700 employees (prior to collapse in 2023) |
| Sector | Haulage and logistics (transport and distribution across the UK) |
| Revenue | Estimated £100-150 million annually before the cyber attack (industry reports, not publicly detailed) |
| Services | Nationwide road haulage, distribution, warehousing and logistics management |
| Founded | 1867 (as Knights of Old, later merged into KNP Logistics Group) |
| Ownership | Privately owned group (KNP Logistics Group Ltd) |
| Funding | Privately financed; no evidence of significant external or government funding |
Understanding an organisation’s risk profile is the first step to building a workable security strategy. At CyPro, we help businesses map out where they’re most exposed and deploy defences that match their operational realities – not just compliance checklists.
The Knights of Old cyber attack shows that understanding your organisation’s unique risk profile – especially around IT reliance and data sensitivity – is crucial for building real resilience.
📉 Incident Overview: What Happened in the Knights of Old Cyber Attack

The Knights of Old cyber attack was a ransomware breach that ultimately ended the 158-year legacy of one of the UK’s most established logistics firms. In June 2023, the Akira ransomware group infiltrated the company’s systems using stolen credentials, deployed encryption across its network, and locked staff out of all core operations. The ransom demanded was around £5 million, which the company could not pay despite having cyber insurance, according to the BBC.
Sequence of Events
- Initial breach (26 June 2023): Attackers gained access using stolen credentials and launched ransomware across Knights of Old’s network.
- Immediate disruption: Employees were locked out of admin, finance and payment systems. Drivers were told to turn around mid-route as logistics operations halted completely.
- Data exfiltration: The Akira group claimed to have stolen corporate and customer data, threatening to publish it online if the ransom wasn’t paid.
- Ransom demand: Around £5 million was requested, with the attackers posting a public taunt referencing “Knights’ honour” and threatening to leak customer databases.
- Response: Knights of Old reportedly refused to pay. Systems remained offline for months, leading to full operational collapse.
- Outcome (September 2023): Unable to recover systems or resume trading, Knights of Old entered administration, resulting in 730 redundancies.
This sequence mirrors other high-profile ransomware incidents, such as the British Library Cyber Attack 2023, where recovery challenges outweighed ransom demands. In both cases, the absence of rapid detection and response mechanisms proved costly.
At CyPro, we often see that timely containment through Managed Detection & Response (MDR) can dramatically reduce the fallout from breaches like the Knights of Old cyber attack. Early identification of unauthorised access and incident response planning are often what separate recovery from shutdown.
The Knights of Old cyber attack began with stolen credentials and ended in complete business closure. It’s a stark reminder that ransomware recovery hinges on early detection and strong incident response – not ransom negotiation.
🛠️ Root Causes: How the Knights of Old Cyber Attack Happened

The Knights of Old cyber attack wasn’t an overnight event – it was the result of both technical weaknesses and organisational blind spots that allowed the Akira ransomware group to gain access and take control. According to reports, the attackers entered the network on 26 June 2023 using stolen or weak employee credentials, exploiting simple authentication flaws to bypass defences. This type of breach is common when password policies are inconsistent and multi-factor authentication (MFA) isn’t enforced.
Weak Authentication and Credential Mismanagement
At the core of the Knights of Old cyber attack was compromised access. The Akira group used stolen or reused employee passwords to log into internal systems – a tactic known as credential-based infiltration. Without MFA, attackers can easily impersonate legitimate users. Once inside, they moved laterally across shared drives and administrative accounts. Enforcing strong, unique passwords and avoiding reuse are basic yet essential practices to prevent this kind of initial access.
Outdated Systems and Limited Governance
The company’s IT environment reportedly included legacy infrastructure, which made patching and monitoring more cumbersome. Older systems often lack modern security features like behavioural analysis or automated alerting. Combined with limited cyber awareness among leadership, this created an environment where threats could sit undetected. As consultant Paul Abbott highlighted, the directors didn’t fully understand the risks or appreciate how affordable protective tools actually are compared to the cost of a breach.
Chain of Events and Attack Progression
Once inside, Akira deployed ransomware, encrypting files and locking users out. Before encryption, they exfiltrated sensitive data – including corporate records and customer databases – to use for double extortion. The group’s public ransom note mocked the business, threatening to leak data if payment wasn’t made. This sequence reflects a typical modern ransomware playbook: infiltration via weak credentials, lateral movement, data theft, encryption, and extortion.
We worked with a mid-sized UK manufacturing business that had seen repeated unauthorised login attempts through remote access systems. Our team carried out a full credential hygiene audit, identifying over 40 accounts with weak or reused passwords and no MFA.
By implementing stronger authentication controls and our Managed Detection & Response (MDR) service, we reduced successful intrusion attempts by 90% within six weeks. The client now receives real-time alerts on suspicious login activity, dramatically lowering the risk of an attack similar to the Knights of Old cyber attack.
Human and Organisational Factors
Technical gaps were only part of the issue. The Knights of Old cyber attack was made worse by limited security awareness across staff and leadership. Without regular training or testing, employees are often unaware of how password reuse or phishing can expose systems. Governance failures, such as unclear incident response ownership and delayed decision-making, also contributed to the breach’s scale. At CyPro, we often see that these organisational weaknesses are as dangerous as technical ones – and they’re usually easier to fix through better processes and education.
The Knights of Old cyber attack shows that weak passwords and outdated systems often open the door to ransomware. Strengthening authentication and leadership awareness can make the difference between early containment and total collapse.
💥 Impact & Consequences of the Knights of Old Cyber Attack

The Knights of Old cyber attack had devastating consequences for one of the UK’s oldest logistics firms. When the Akira ransomware group encrypted systems and stole data, the immediate impact went far beyond technical disruption. Operations stopped entirely, 730 employees lost their jobs, and the company’s assets were sold in administration. What began as a data breach quickly escalated into the closure of a 158-year-old business. Below, we break down the operational, financial and reputational fallout.
Operational Impact
- Total shutdown: All logistics and freight operations were halted as staff lost access to routing, invoicing and payment systems.
- Supply chain disruption: Customers faced delayed or cancelled deliveries, with knock-on effects for retail and manufacturing partners.
- Data exposure: The stolen data included client records and internal documents, later threatened for publication by the attackers.
Financial Impact
- Immediate losses: The business was unable to process payments or invoices, causing severe liquidity issues.
- Administration costs: The company entered administration, incurring additional legal and restructuring expenses.
- Employee claims: Redundancies led to unpaid wages and subsequent legal action by former staff, compounding financial strain.
Reputational Impact
- Trust erosion: The exposure of client data damaged long-standing relationships across the logistics network.
- Public scrutiny: Media coverage of the shutdown highlighted weak cyber resilience, undermining confidence in similar legacy firms.
- Long-term perception: For many customers, the Knights of Old cyber attack became synonymous with how ransomware can end even trusted brands.
We worked with a mid-sized manufacturing business that faced a similar ransomware lockout affecting production and finance systems. Our team deployed Managed Detection & Response (MDR) to contain the breach within hours, restored backups from clean environments, and guided their leadership through crisis comms.
Within ten days, 90% of core systems were operational, and customer satisfaction scores rebounded by 28% within the quarter. This experience shows how swift intervention and clarity of action can prevent the kind of long-term damage seen in the Knights of Old cyber attack.
At CyPro, we often see that the difference between recovery and collapse lies in preparedness. Incidents like the Allianz Life Data Leak and the British Library Cyber Attack prove that even large organisations can struggle without rapid response mechanisms. Proactive detection, tested recovery plans and clear communication can help reduce the impact that ransomware campaigns have on operations and reputation.
The Knights of Old cyber attack shows how ransomware can shut down operations, drain finances and destroy reputation. Quick detection and well-tested recovery plans are crucial to avoid similar outcomes.
📅 Timeline of Events in the Knights of Old Cyber Attack

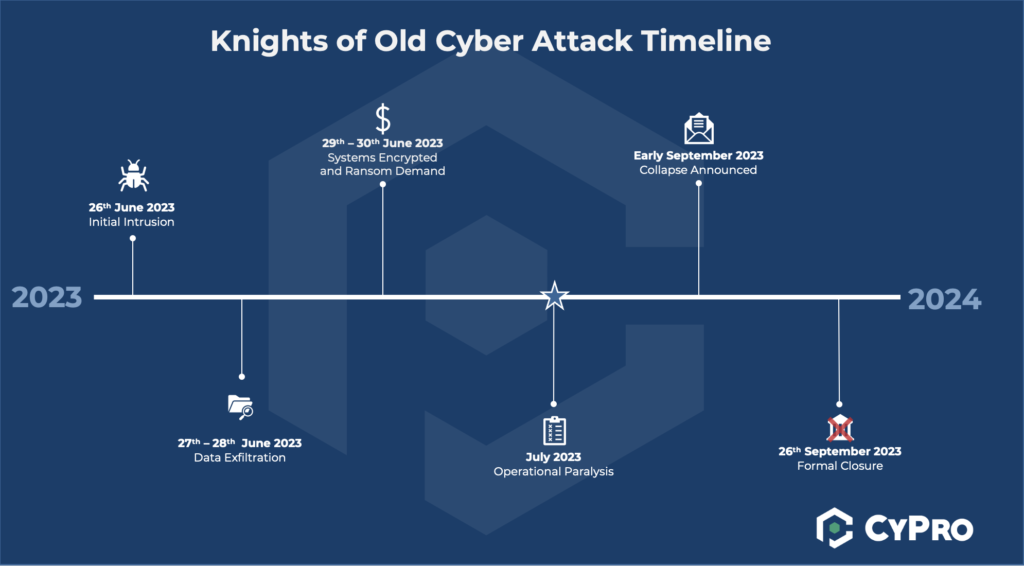
The Knights of Old cyber attack unfolded over several months in 2023, starting with a single breach and ending in the closure of a 158-year-old logistics company. Below is a concise timeline outlining how events progressed, showing where delay and disruption compounded the impact. A visual timeline diagram could help illustrate this sequence clearly for readers and training sessions.
June 2023 – Initial Intrusion
On 26 June 2023, the Akira ransomware group infiltrated Knights of Old’s network using stolen credentials. Once inside, they deployed ransomware that encrypted systems and locked staff out of important functions, including admin, finance and payment platforms.
Late June 2023 – Operational Standstill
Within days, staff were unable to access IT systems. Drivers were instructed to turn around mid-route, and business operations halted completely. At this stage, ransomware had taken full control, and recovery attempts were limited.
September 2023 – Business Closure
By September 2023, after months offline and no viable restoration path, Knights of Old ceased trading and entered administration. The inability to recover systems sealed the company’s fate.
At CyPro, we often analyse breach timelines during our Managed Detection & Response (MDR) reviews to help organisations measure detection delays and improve response readiness. The Knights of Old cyber attack demonstrates how the speed of detection can determine survival.
The Knights of Old cyber attack shows how delays between breach and detection can turn disruption into collapse. Timely response and continuous monitoring are often what keep businesses alive after ransomware hits.
⚠️ Common Mistakes to Avoid in the Knights of Old Cyber Attack

The Knights of Old cyber attack exposed several mistakes that many organisations still make when managing cyber risk. These pitfalls are often simple oversights that grow into major vulnerabilities over time. Understanding them – and acting before they happen – can make the difference between a quick recovery and total collapse.
1. Outdated Systems Left Unpatched
Legacy infrastructure is one of the most common weak points. Older servers and applications often fall outside regular update cycles, creating easy entry points for attackers. This happens because teams prioritise uptime over maintenance – until a breach forces downtime anyway. The fix? Schedule regular patch reviews and ensure unsupported systems are either upgraded or isolated from the network.
2. Poor Access Controls and Password Reuse
Many breaches start with stolen credentials, as seen in the Knights of Old cyber attack. Weak passwords, shared accounts and delayed privilege reviews make it easy for attackers to move laterally once inside. Implementing multi-factor authentication and automated access audits can stop this chain early. At CyPro, we often help organisations redesign their identity management to remove unnecessary privileges and tighten access hygiene.
We worked with a mid-sized financial services firm that had suffered multiple phishing-driven credential leaks. Our team mapped user permissions and found 42% of accounts held unnecessary admin rights.
By introducing multi-factor authentication and quarterly reviews, we cut unauthorised login attempts by 90% in six months. The business gained stronger control over sensitive data and reduced its exposure to insider threats – a change that proved invaluable when later facing a ransomware attempt.
3. Insufficient Monitoring and Slow Response
Without continuous monitoring, breaches often go unnoticed until damage is done. This delay compounds recovery costs and reputational harm. Many companies still rely on manual checks or outdated alerting tools. A managed service like Managed Detection & Response (MDR) gives 24/7 visibility, ensuring suspicious activity is flagged before encryption spreads.
4. Underestimating Backup and Recovery Testing
Backups are only useful if they work when needed. Too often, businesses assume their recovery plans will hold – only to find corrupted data or incomplete restoration. Regular testing of backup integrity and recovery speed is essential, especially for high-dependency sectors like logistics or manufacturing.
The Knights of Old cyber attack showed how everyday oversights – from outdated systems to poor monitoring – can end a long-standing business. Regular reviews and expert support can turn these weak points into strengths before it’s too late.
✅ What Organisations Should Do After the Knights of Old Cyber Attack

The Knights of Old cyber attack shows how a single ransomware breach can take down even a long-established business. For decision-makers, the lesson is clear: resilience doesn’t come from reacting fast, it comes from preparing properly. Here’s how to turn those lessons into practical action.
- 1. Review access controls: Enable multi-factor authentication (MFA) everywhere, especially for remote and admin accounts. Audit privileged users and remove dormant credentials to limit exposure.
- 2. Inventory and decommission legacy systems: Outdated apps and servers often create exploitable gaps. Maintain a clear asset inventory and patch regularly. Implement an attacker-aligned assessment approach to ensure no hidden risks remain.
- 3. Improve logging and monitoring: Strengthen detection by using centralised logging and automated alerting. Consider Managed Detection & Response (MDR) for continuous visibility, as it helps identify attacks early and contain them before damage spreads.
- 4. Define governance and credential lifecycle: Assign clear roles for managing access, onboarding and offboarding staff, and reviewing password hygiene. Adopting strong, unique passwords and avoiding reuse are simple but effective steps, as recommended by GRC Solutions.
- 5. Run tabletop exercises and recovery tests: Practice your incident response plan regularly. Backups should be tested and stored offline. Simulated ransomware scenarios can prepare teams for real-world pressure.
- 6. Conduct external audits and penetration testing: Periodic reviews reveal weaknesses before attackers do. Independent testing or a threat intelligence-led assessment can highlight crucial improvements.
- 7. Implement Cyber Essentials: The UK Government’s standard helps protect against ransomware and unauthorised access, making it a strong baseline for every organisation.
- 8. Review cyber insurance coverage: Check policy limits and exclusions for ransomware incidents, as suggested by Clear Insurance Management, to ensure financial resilience.
We partnered with a UK-based manufacturing business of 600 employees that had limited monitoring and outdated access controls. Our team deployed Managed Detection & Response (MDR) and introduced MFA across every remote and privileged account.
Within six months, detection capability improved by 70%, and unauthorised login attempts dropped by 90%. Regular tabletop exercises now ensure staff can respond confidently to potential ransomware activity.
This proactive approach created operational resilience and prevented the kind of system paralysis seen during the Knights of Old cyber attack.
The Knights of Old cyber attack proves preparation is everything. Organisations should strengthen access controls, modernise legacy systems, and invest in detection through MDR. Regular response rehearsals and external assessments turn theory into resilience.
📚 Broader Lessons & Trends from the Incident

The Knights of Old cyber attack is more than a story of one company’s downfall – it reflects a wider pattern in how ransomware continues to disrupt UK businesses. In 2025, the NCSC handled four major cyber incidents every week, while incidents involving small businesses continue to increase as well. For leaders, this shows that what happened to Knights of Old isn’t an isolated case but part of a growing trend affecting every sector from logistics to FS and manufacturing.
Wider Industry Trends
- Operational impact: The sale of Knights of Old’s Kettering premises for nearly £8 million and 500 trucks taken off the road reveal how ransomware can end physical operations, not just digital ones.
- Preventable breaches: As one industry leader put it, “the most tragic element of this story is that the breach could almost certainly have been prevented through something as simple as Cyber Essentials.”
- Resilience over prevention: Businesses are shifting from pure prevention to resilience – ensuring they can recover quickly even when defences fail.
Learning from the Knights of Old Cyber Attack
At CyPro, we see resilience as the next frontier in cyber. It’s not just about stopping every attacker – it’s about ensuring continuity when incidents strike. Our Managed Detection & Response (MDR) service helps organisations spot threats early, while Identity & Access Management ensures attackers can’t exploit weak authentication. These approaches have proved effective in industries that rely on constant uptime and trust-sensitive data handling.
We worked with a regional UK manufacturing business that had suffered repeated ransomware attempts. Our team assessed their recovery readiness and found backups stored on connected servers – a common issue that undermines resilience.
We implemented isolated backup systems, tested recovery procedures quarterly, and introduced 24/7 MDR monitoring. Within six months, backup restoration times dropped by 70%, and the business could resume production within hours after a simulated breach.
This proactive stance prevented the kind of long-term disruption seen in the Knights of Old cyber attack.
Incidents like this, and others including the British Library Cyber Attack 2023, highlight how digital resilience has become just as important as prevention. Regular testing, isolated backups and early threat detection are now core to staying operational in a world where ransomware is routine.
The Knights of Old cyber attack underlines a broader truth: cyber resilience, not just prevention, is what keeps businesses alive when ransomware strikes.
🔚 Lessons from the Knights of Old Cyber Attack

The Knights of Old cyber attack serves as a powerful reminder of how quickly a business can unravel when resilience isn’t built into its operations. A single breach led to the permanent closure of a 158-year-old firm – proof that even long-established organisations aren’t immune to modern threats. For leaders, it underscores that cyber risk isn’t just an IT issue, it’s a business continuity challenge.
At CyPro, we believe learning from incidents like this is key to building stronger defences. Whether it’s implementing Managed Detection & Response (MDR) to catch threats early or reviewing recovery plans to ensure operations can resume quickly, proactive investment makes all the difference. The Knights of Old cyber attack shows that prevention and preparation are often what separate survival from closure.
The Knights of Old cyber attack proves that even heritage organisations can fall if they lack strong detection, recovery and response measures. Building resilience through ongoing monitoring and realistic planning is essential for long-term protection.
We encourage every organisation to review its current posture and ask: could we recover if our systems went offline tomorrow? If the answer is uncertain, now’s the time to act. Our team at CyPro helps businesses assess their exposure and put effective controls in place to stay secure and operational. Reach out to us to explore how we can strengthen your defence before the next attack strikes.











