Table of Contents
Small and medium-sized businesses (SMBs) face increasing pressures to strengthen their cyber security. Cyber threats have become more frequent, more sophisticated and more targeted, especially against organisations with limited internal resources. Many SMBs operate with a false sense of security, assuming their systems are protected until a breach proves otherwise. Building cyber resilience starts by getting honest about what’s really in place today.
Despite constant headlines about ransomware and phishing, many SMEs still treat cyber security as an IT issue rather than a business one. It’s understandable as when you’re focused on customers, cash flow and growth, security often slips down the list. But cyber risk behaves more like cholesterol: invisible until it causes real damage. Regular assessment doesn’t just find vulnerabilities; it uncovers habits, outdated software and process gaps that quietly weaken your business from within.
A cyber risk assessment changes that. It gives your business a clear understanding of its true cyber posture, revealing vulnerabilities, outdated processes, inconsistent controls and areas where attackers are most likely to strike. It helps you prioritise actions that make a real difference to cyber resilience, compliance and operational continuity.
In the UK, the National Cyber Security Centre (NCSC) highlights phishing and supply-chain compromise as persistent threats for small firms. Even modest IT setups can be compromised through a weak password, a single employee clicking the wrong link, or a supplier with poor controls. A cyber risk assessment exposes those risks early, strengthens cyber resilience and shows exactly where your cyber posture is weakest, before they become expensive lessons.
A cyber risk assessment is your business’s health check. Without it, you’re training blind, guessing your weaknesses and leaving yourself open to a cyber injury.
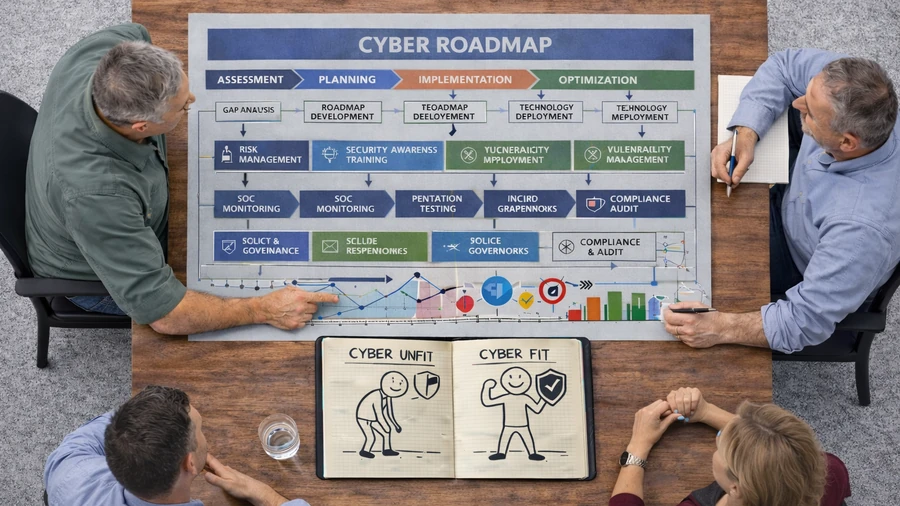
And just like improving physical fitness, strengthening your cyber security doesn’t happen all at once. It happens through clear steps: understanding where you stand today, creating a practical plan, building capability over time, preventing costly incidents and tracking your progress so you don’t slip backwards.
In this guide, we’ll break down these five steps to help SMBs build lasting, measurable cyber resilience, one improvement at a time.

🔎 Step One – Understand Your Current Cyber Posture
Every effective cyber security programme begins with visibility. If you don’t know where your vulnerabilities lie, you can’t prioritise what matters. A cyber risk assessment provides SMBs with an honest, comprehensive view of their current cyber posture.
This involves:
- Evaluating systems, networks and applications for weaknesses
- Reviewing access controls, user behaviour and permissions
- Checking the maturity of policies and governance
- Identifying gaps in backup, incident response and monitoring
- Benchmarking controls against recognised standards like Cyber Essentials or ISO 27001
For many SMBs, the risk assessment uncovers issues that were previously unknown: dormant admin accounts, outdated software, unmanaged third-party integrations or shadow IT introduced by staff.
Just as a fitness assessment identifies areas for improvement, this step helps businesses prioritise cyber risks based on likelihood and impact, ensuring resources are invested wisely.
A University of Greenwich study (2024) examined how a UK SME used a formal cyber risk assessment to evaluate its exposure. Despite limited internal cyber expertise, the business identified vulnerabilities in cloud configurations, user access permissions and third-party tools. By mapping digital assets and prioritising risks, the company implemented targeted improvements such as strong access controls, structured updates and clearer governance processes, showing how much progress SMBs can make simply by understanding their baseline.
You can’t improve what you don’t measure. A cyber risk assessment gives you that measurement by being the fitness tracker for your business’s cyber health.
🎯 Step Two – Define Your Target Cyber State
Before you can design an effective cyber security plan, you need to be clear about what you’re aiming for. Different SMBs require different levels of cyber resilience depending on size, sector, regulation and risk appetite. Defining a target state keeps your risk-based security programme aligned to what the business actually needs. Your target state should be realistic but resilient, strengthening cyber resilience without creating an unmanageable programme.
Some businesses aim to meet baseline standards like Cyber Essentials Plus. Others need more advanced cyber resilience to win contracts, handle sensitive data or support future growth. A few may want to mature toward ISO 27001 alignment or a more formalised governance model. What matters is choosing a target that fits your organisation’s realistic needs and resources.
This is similar to defining your level of desired fitness. Some people train for elite competition; others simply want to feel healthier, move better or shed the “dad bod.” The goal determines the programme, not the other way around.
Once your target state is clear, you can identify the capabilities, controls and cultural changes required to close the gap between where you are today and where you need to be. Without this step, cyber improvements risk becoming fragmented or misaligned with the business.
What defining your target state typically includes:
- Determining the maturity level you want to reach (e.g., basic, intermediate or advanced)
- Understanding compliance requirements (e.g., CE+, FCA, ISO, contracts)
- Assessing your risk appetite
- Identifying the level of monitoring and response you expect
- Setting expectations for staff awareness and governance
- Agreeing timelines and investment boundaries
Why this matters:
A clear destination ensures that your cyber roadmap is purposeful, achievable and tailored to your business. You avoid unnecessary spending while ensuring you’re building toward the right level of cyber resilience.
You can’t design an effective security strategy without knowing your desired end state. Define your goals first, then build the plan to get there.
🧩 Step Three – Build a Tailored Cyber Security Plan
Once you’ve defined your target cyber posture, the next step is to design a security plan that will get you there. Your risk assessment should drive the order of work so you fix what matters most first. The most effective plans are based on proven frameworks and one of the most widely used is the NIST Cyber Security Framework (CSF).
The NIST CSF breaks cyber security into practical domains that help SMBs organise their improvements in a clear, structured way.
Using these domains ensures that your plan isn’t just a list of tasks but a balanced programme that strengthens governance, controls, monitoring and response in coordinated, sustainable manner.
Here’s how SMBs can use the NIST domains to structure their plan:
1. GOVERN – Set the direction and accountability
This creates the foundation for your entire security programme.
Activities may include:
- Defining responsibilities and escalation paths
- Documenting policies and standards
- Aligning leadership on risk appetite and priorities
- Ensuring suppliers and partners meet minimum requirements
In fitness terms, this is deciding your training regime, schedule and accountability.
2. IDENTIFY – Understand what needs protecting
This focuses on visibility by knowing what assets, systems, data and dependencies exist.
Typical actions include:
- Mapping your digital assets
- Identifying sensitive or critical data
- Understanding systems, devices and third-party tools
- Assessing business-critical processes
Like knowing which muscle groups need the most focus, IDENTIFY shows where to apply effort.

3. PROTECT – Strengthen preventative controls
These are the safeguards needed to reduce the likelihood of a cyber incident.
Actions may include:
- Multi-factor authentication (MFA)
- Access control enhancements
- Device and software hardening
- Patch management
- User awareness and phishing training
- Data protection and encryption controls
In fitness terms, PROTECT is about strengthening core muscles by making the whole body more resilient.
4. DETECT – Spot issues early
This focuses on monitoring and alerting so threats don’t go unnoticed.
Actions may include:
- Log collection and analysis
- Endpoint monitoring
- Email threat detection
- Automated alerting
- Behaviour anomaly detection
- Affordable MDR (Managed Detection & Response) services
DETECT is the equivalent of tracking heart rate or performance metrics during a workout by catching issues early.

5. RESPOND – Act quickly when something goes wrong
Effective response limits damage and reduces downtime.
Actions may include:
- Documented incident response procedures
- Clear contact routes and decision-making thresholds
- Communication plans for internal and external stakeholders
- Rapid isolation of affected devices or accounts
Like adjusting form in the middle of a workout, RESPONDing fast prevents injury.
6. RECOVER – Get the business back on its feet
This ensures your business can quickly return to normal operations after an incident.
Actions may include:
- Reliable, tested backups
- Restoration procedures
- Lessons-learned reviews
- Improving controls after incidents
- Insurance and continuity planning
RECOVERy in fitness is as important as exertion as it prevents long-term damage.
Using the NIST CSF gives SMBs a clear, credible structure for building a security plan – one that strengthens governance, prevention, detection and recovery in a balanced and achievable way.
🏗️ Step Four – Build Capability and Resilience Over Time
No one gets fit after one gym session. The same goes for cyber security. True resilience comes from consistent effort of checking progress, adjusting routines and keeping motivation high.
Once your risk assessment is complete, the challenge becomes maintaining momentum. That means quarterly reviews, refresher training and routine testing. Many small businesses choose affordable Managed Detection and Response (MDR) services to monitor threats continuously, while others run internal drills to ensure their incident plan works under pressure.
Culture plays a huge role too. Technology protects systems, but only people can protect information. Teaching your team to recognise phishing, spot suspicious emails and follow process is like teaching athletes proper form; it prevents injury before it happens.
According to the Cyber Security Breaches Survey 2024, nearly half of UK small businesses suffered a cyber breach or attack in the past year, with phishing and human error among the leading causes. Regular risk assessments identify those risky habits and fix them early.
Strength comes from consistency. Repetition, monitoring and continuous improvement turn cyber security from a project into a habit.
Measuring progress doesn’t just benefit IT, it boosts confidence across the business. Monthly “cyber health” reports showing fewer vulnerabilities or faster response times make improvement visible. Recognising teams who report phishing attempts or flag weaknesses keeps engagement high and reinforces that security is everyone’s responsibility.
In 2022, KP Snacks, a major UK manufacturer, suffered a ransomware attack that disrupted production and supply chains for weeks. Systems were encrypted, orders halted and distribution delayed. Although KP Snacks is larger than most SMEs, the incident illustrates how a single disruption can paralyse operations. For smaller firms, a comparable event could be existential. Regular assessments and response testing are vital to avoid similar downtime.
🧯Step Five – Prevent Cyber Incidents Before They Happen
Anyone who’s ever pulled a muscle knows the pain of skipping a warm-up. In cyber security, the equivalent injury of a data breach or ransomware attack can cripple a small business.
Breaches are expensive, disruptive and often avoidable. Prevention is always cheaper than recovery, and for SMBs the difference can be existential. The IBM Cost of a Data Breach Report 2024 shows that UK organisations face average breach costs of £3.6 million, the highest in Europe. For a small business, the operational downtime, reputational damage and financial impact can be overwhelming.
Strong cyber hygiene is your early defence. Keeping systems updated, removing unused accounts, enforcing strong passwords, validating backups and reviewing third-party access all reduce the chances of a breach long before attackers get near your systems.
It’s similar to maintaining flexibility and stretching properly before exercise, small, simple habits that dramatically reduce the risk of serious injury. In the same way athletes use mobility work to prevent strains or tears, SMBs can use good hygiene practices to prevent vulnerabilities from turning into costly incidents.
British retailer FatFace suffered a ransomware attack in 2021 that exposed customer and employee data. The company had to notify affected individuals and reportedly paid a ransom to regain control. The incident shows that even well-known consumer brands can be caught off guard and for smaller businesses with limited budgets, prevention through regular assessment is far cheaper than recovery after a breach.
Skipping the small things leads to injury. Prevention through regular cyber risk assessments and audit cycles saves time, money and reputation.
📊 Step Six – Measure Progress and Stay Accountable
Cyber security isn’t a one-time achievement; it’s an ongoing performance discipline. As your business grows, adopts new technologies and faces emerging threats, your security posture must evolve in parallel. Your cyber posture should keep pace too, because without regular measurement your cyber resilience erodes quietly over time and risk-based security turns into guesswork
To stay resilient, SMBs need clear ways to measure whether their cyber capability is improving. These measurements fall into three practical categories: strategic, operational and tactical.
Together, they give a balanced view of how well your organisation is performing – just as athletes assess overall progress using a combination of long-term goals, training quality and daily performance metrics.

Strategic Metrics – Are we becoming more mature over time?
These focus on long-term, organisation-wide progress and help leadership understand whether cyber security is strengthening year after year. Examples include:
- Cyber maturity assessments (e.g., Cyber Essentials Plus, NCSC CAF, ISO alignment)
- Risk exposure trends (high -> medium -> low)
- Governance and policy adoption rates
- Supplier assurance status
These are the equivalents of long-term fitness indicators – body composition changes, mobility improvements, or overall strength gains.
Operational Metrics – Are our core processes working effectively?
These measure the quality and consistency of your ongoing security activities and controls. Examples include:
- Vulnerability management performance (age and volume of open vulnerabilities)
- Patching frequency and completion rates
- Backup reliability and restoration testing results
- User awareness performance (phishing simulations, training completion)
Just as athletes track workload, technique and training efficiency, operational metrics show how well your security routines are functioning day-to-day.


Tactical Metrics – How fast and effectively can we react?
These are real-time performance indicators that show how well you detect and respond to threats in practice. Examples include:
- Mean Time to Detect (MTTD)
- Mean Time to Respond (MTTR)
- Containment and eradication times
- Incident volume, severity and recurrence
Think of these as sprint times or reaction drills in sport – the indicators that reveal speed, agility and readiness.
Why these three levels matter
No single measurement gives the full picture – just as athletes rely on a mix of strength tests, endurance scores and power metrics.
By combining strategic, operational and tactical measurements, SMBs get a balanced, data-driven view of their security performance and can make informed decisions about where to focus next.
Mature cyber programmes measure performance at all three levels: long-term maturity, day-to-day control quality and real-time incident capability.
💪 Conclusion – Train Smart, Stay Strong
These are the practical principles that apply equally in cyber security and in fitness, because progress comes from structure, consistency and steady improvement.
Set Achievable, Incremental Objectives
- You wouldn’t train for an ultra-marathon on day one. Likewise, SMBs shouldn’t try to “fix everything at once.”
- Cyber resilience is built through realistic goals: closing your highest-risk vulnerabilities first, improving access control step by step, or rolling out MFA across core systems before expanding further.
Measure What Matters
- Athletes track body composition, VO₂ max, speed and power because data drives progress.
- In cyber, metrics such as MTTD, patching rates, phishing resilience and backup success give you the insight needed to improve and maintain performance.
Build Good Habits to Drive Discipline
- Small, consistent habits have a bigger long-term impact than dramatic, one-off efforts.
- In cyber terms, that means regular updates, routine reviews, simple daily hygiene, and embedding awareness into working culture.

Consistency Beats One-Off Effort
- Fitness improves through repetition, showing up, session after session.
- Cyber security works the same way. Regular assessments, continuous monitoring and recurring training have far greater impact than a single technology deployment.
Stay Adaptable as Conditions Change
- As athletes progress, their training evolves with more load, more intensity, different techniques.
- Cyber threats evolve too. Your controls, policies and monitoring need to adapt to new digital risks, growth, and changes in the business environment.
Recovery and Readiness Matter as Much as Strength
- In fitness, recovery prevents injury. In cyber, preparation prevents downtime.
- Testing backups, rehearsing incident response and ensuring failover capability protects your business when something goes wrong.
Cyber security is ultimately about discipline, not drama. A cyber risk assessment gives SMBs the clarity they need to get started: a realistic understanding of where their weaknesses lie, which improvements matter most and how to prioritise limited resources. From there, resilience develops through measurable improvements, good habits, repeatable processes and a willingness to adapt as threats evolve.
Just as athletes build capability by showing up, refining technique and testing their performance regularly, SMBs strengthen their cyber posture by reviewing risks, training their teams, validating controls and acting before small issues become major incidents.
As the new year unfolds, small businesses will continue to face challenges from AI-powered scams, supply-chain risks and credential theft. The ones that stay “cyber fit” will be those that keep assessing, learning and adjusting. Your personal trainer wouldn’t let you skip a session, nor should your IT team.
Cyber resilience isn’t built through tools or technology alone, it’s built through mindset, discipline and consistent improvement.
If your business is ready to build stronger cyber foundations, CyPro’s experts can run a practical risk assessment to baseline your cyber posture and create a risk-based security roadmap that improves protection step by step and keeps you resilient long-term.











