Table of Contents
🔍 Introduction to SOCs in Cyber Security
In today’s fast-moving digital world, staying ahead of threats is a constant challenge for any organisation. A Security Operations Centre (SOC) is at the heart of a strong cyber security strategy. It’s a dedicated team and set of technologies that continuously monitor, detect and respond to suspicious activity. When we talk about SOC cyber security, we’re talking about this round-the-clock capability to spot problems before they escalate.
At CyPro, we know how demanding it can be for businesses to keep pace with evolving threats and compliance expectations. A SOC provides 24/7 monitoring and response to security incidents, as confirmed by Microsoft. That means potential breaches can be identified and handled fast, reducing damage and downtime. Our own team, including analysts like Josh Lipscombe, work hands-on with clients to strengthen detection and response processes through services such as SOC as a Service and Managed Detection & Response (MDR).
In this post, we’ll unpack what a SOC actually is, why it matters and how it fits into your broader cyber security plans. By the end, you’ll understand how a SOC cyber security approach can improve resilience, visibility and confidence across your organisation.
🔐 What Is a SOC in Cyber Security?

A Security Operations Centre (SOC) in cyber security is like a digital control room for your organisation’s security. It’s where trained analysts and automated tools work together to spot, investigate and respond to suspicious activity in real time. Think of it as the equivalent of a 24/7 alarm system and response team for your IT environment – always awake, always watching, and ready to act before a small issue becomes a major incident.
The core purpose of a SOC is to keep your business safe by continuously monitoring networks, servers and devices. This visibility means threats can be detected early, reducing risk and downtime. It also enables your wider cyber security strategy to be proactive rather than reactive. Instead of waiting for something to go wrong, the SOC hunts for signs of trouble – unusual logins, strange data transfers or system anomalies – and responds quickly to contain them.
At CyPro, we build and run SOCs that integrate seamlessly with services like Cyber Security as a Service and SOC 2 Compliance, helping organisations maintain strong assurance and meet regulatory standards. Our analysts use advanced tools and automation to streamline detection and response, ensuring round-the-clock protection. Whether you manage your own SOC or use our SOC as a Service model, the goal is the same: to give you constant oversight and peace of mind.
In short, adopting a SOC cyber security approach means you have a dedicated team and technology stack focused entirely on safeguarding your digital assets – an essential part of any modern business operation.
A SOC acts as your organisation’s always-on security nerve centre, combining people, processes and technology to detect and respond to threats before they cause harm.
⚡ Why It Matters

Investing in a SOC cyber security capability isn’t just about ticking a compliance box – it’s about protecting your organisation’s reputation, assets and bottom line. With attacks becoming more frequent and sophisticated, a SOC gives you the visibility and confidence to act fast when something looks wrong. It’s increasingly expected by regulators, insurers and clients alike as proof that you take data protection seriously.
- Reduce risk: Continuous monitoring means threats are spotted early, minimising downtime and financial loss.
- Strengthen compliance: A SOC supports frameworks like ISO 27001 and SOC 2, helping meet growing customer and regulatory expectations.
- Cut costs: Automated detection and efficient response save money by reducing incident recovery time.
- Improve trust: Demonstrating proactive defence helps win new business and keep existing clients confident.
- Stay competitive: As seen in telecoms and FS sectors, those who invest in proactive SOC operations gain a market edge.
We worked with a UK-based manufacturing business that had experienced repeated phishing and ransomware attempts. With no dedicated SOC, incidents were taking days to resolve, causing production delays and rising costs.
Our team deployed our SOC as a Service solution to deliver round-the-clock monitoring and automated incident triage. Within three months, mean detection time fell by 70% and response speed improved by over 60%.
The business avoided two serious breaches, lowered insurance premiums and gained the assurance needed to meet new client security requirements – turning what was once a reactive process into a proactive defence model.
At CyPro, we help you build or enhance your SOC through services like Cyber Security as a Service and Embracing the March 2027 telecoms Security Act (TSA) Requirements. These solutions bring together technology, expertise and 24/7 oversight so you’re ready for whatever the next wave of threats brings.
🧩 Key Components of a SOC

A strong SOC cyber security setup relies on four main pillars: processes, controls, tools and technology, and people. Each works together to keep your organisation secure, coordinated and ready to respond when threats appear. Below, we break down the essential building blocks that make up a well-functioning Security Operations Centre.
🔄 Processes
Effective processes form the backbone of how a SOC operates day to day. They define how threats are detected, assessed and contained, ensuring consistency and speed.
- Incident detection and triage: Identifying suspicious activity within minutes rather than months, as highlighted by IT By Design.
- Incident response: Coordinating containment, eradication and recovery actions instead of isolated, disjointed responses – a point stressed by Logicalis.
- Threat hunting: Proactively searching for hidden risks before they cause harm.
- Vulnerability management: Applying patches and addressing misconfigurations to reduce the attack surface, supported by Microsoft.
- Reporting and continuous improvement: Reviewing outcomes to refine detection rules and enhance future readiness.
🧱 Controls
Controls are the safeguards that ensure processes run securely and efficiently. A mature SOC uses layered controls to protect data and maintain operational integrity.
- Access control: Managing who can view, change or act on incidents.
- Segregation of duties: Preventing conflicts by separating detection, analysis and remediation tasks.
- Audit and compliance checks: Ensuring logs and actions meet standards like ISO 27001 and SOC 2.
- Asset management: Keeping a live inventory of systems and software for visibility across the IT estate.
- Patch enforcement: Using automated workflows to maintain system hygiene and minimise risk exposure.

⚙️ Tools and Technology in SOC Cyber Security
Technology is what enables a SOC to operate around the clock and respond at scale. Modern SOC cyber security environments combine automation, intelligence and integration.
- SIEM platforms: Collect and analyse logs from across your network to detect anomalies.
- Endpoint detection and response (EDR): Tools like SentinelOne help analysts spot malicious behaviour on devices before it spreads.
- Threat intelligence feeds: Provide up-to-date indicators to enrich analysis.
- Automation and orchestration: Streamline repetitive tasks and speed up incident handling.
- Monitoring dashboards: Give real-time visibility into alerts, trends and performance metrics.
At CyPro, we integrate these technologies within our Cyber Security as a Service and SOC as a Service offerings, providing clients with continuous oversight and rapid response capabilities.
👥 Roles and Responsibilities
People are the core of any SOC. Skilled analysts, engineers and managers ensure the technology works effectively and incidents are handled correctly.
- SOC Analysts: Monitor alerts, investigate suspicious behaviour and perform initial response actions.
- SOC Engineers: Build and tune detection rules, maintain integrations and enhance automation – roles often led by experts across CyPro.
- Incident Responders: Lead containment and recovery efforts following confirmed breaches.
- Threat Hunters: Actively search for vulnerabilities and abnormal patterns.
- Management and Leadership: Oversee operations, align with business goals and ensure compliance with internal and external frameworks.
These roles form a coordinated defence, ensuring that every aspect of your SOC cyber security operation contributes to reducing risk and improving resilience.
A well-built SOC combines structured processes, strong controls, smart tools and skilled people. Together, these components create a responsive, coordinated defence that strengthens your overall soc cyber security posture.
📊 Maturity Levels of SOCs in Cyber Security

When it comes to SOC cyber security, maturity isn’t just about how long a SOC has existed. It’s about how well it integrates people, process and technology to deliver consistent, measurable protection. Most organisations move through four maturity stages – from ad hoc monitoring to a fully optimised operation that uses automation and threat intelligence to stay ahead.
🔼 Typical SOC Maturity Stages
| Stage | What It Looks Like | Indicators |
|---|---|---|
| 1. Ad hoc | Reactive security, no formal SOC. Incidents are handled manually when noticed. | Limited visibility, inconsistent response, reliance on external help. |
| 2. Defined | Basic monitoring tools in place, some documented processes. | Alerts are reviewed, but investigation and response remain manual. |
| 3. Managed | Dedicated SOC team, structured processes and technology integration. | Consistent reporting, measurable response times, 24/7 coverage via Cyber Security as a Service or managed SOC. |
| 4. Optimised | Automation, threat hunting and intelligence-led operations. | Continuous improvement, predictive capability, integration with compliance frameworks like SOC 2 Compliance. |
We often see organisations progress as their business grows or following major incidents. Many move from “defined” to “managed” maturity by adopting services such as SOC as a Service or Managed Detection & Response (MDR). According to Logicalis, using a managed SOC helps bridge skills gaps and gives access to the latest threat intelligence – a crucial step in maturity development. Our analysts regularly support clients through this transition, helping them build confidence and operational consistency.
As maturity grows, performance moves from reactive to proactive. A mature SOC doesn’t just respond – it anticipates, learns and adapts. That’s what “good” looks like in SOC cyber security.
A mature SOC in cyber security combines automation, intelligence and skilled analysts to deliver proactive defence and continuous improvement. If you’re still operating reactively, it’s time to move towards a managed or optimised model – something we can help you achieve at CyPro.
⚠️ Common Mistakes to Avoid in SOC Cyber Security

Building or managing a SOC cyber security capability isn’t easy. Many organisations jump in without fully understanding what’s involved, leading to inefficiencies, wasted investment and poor response times. Here are a few pitfalls we often see and how to avoid them.
- Underestimating resource needs: A SOC demands people, processes and technology working together around the clock. Many teams assume tools alone will do the job, but without trained analysts and clear procedures, alerts go uninvestigated. It’s crucial to plan for ongoing staffing and skill development from day one.
- Confusing compliance with security: Some businesses treat SOC implementation as purely a compliance exercise, focusing on ticking boxes like SOC 2 or ISO 27001. Compliance helps, but genuine protection needs active monitoring and threat hunting, not just paperwork.
- Poor integration with existing systems: A SOC must fit seamlessly into your IT environment. Failing to connect data sources properly leads to blind spots and missed alerts. Engage experienced engineers early who know how to design detection rules and integrate SIEM tools effectively.
We worked with a mid-sized FS firm that had launched a new SOC but struggled to respond to incidents effectively. They’d invested heavily in tools but had no clear workflow or trained analysts.
As a result, alerts piled up and genuine threats were missed. We revamped their processes, trained internal staff and integrated their SOC with our Managed Detection & Response (MDR) service.
Within six months, alert resolution times dropped by 65% and false positives decreased by half. The firm now has a leaner, faster and more confident security operation supported by our ongoing oversight.
At CyPro, we help businesses avoid these common mistakes through hands-on design and continuous support. Whether you’re building in-house or using our SOC as a Service model, we make sure your SOC delivers real protection – not just compliance. For more on aligning technical controls with regulatory goals, see Embracing the March 2027 telecoms Security Act (TSA) Requirements.
A successful SOC cyber security strategy needs more than tools – it demands skilled people, integrated systems and a clear operational plan to turn alerts into action.
🗺️ Framework Mapping: How SOC Cyber Security Connects to Standards
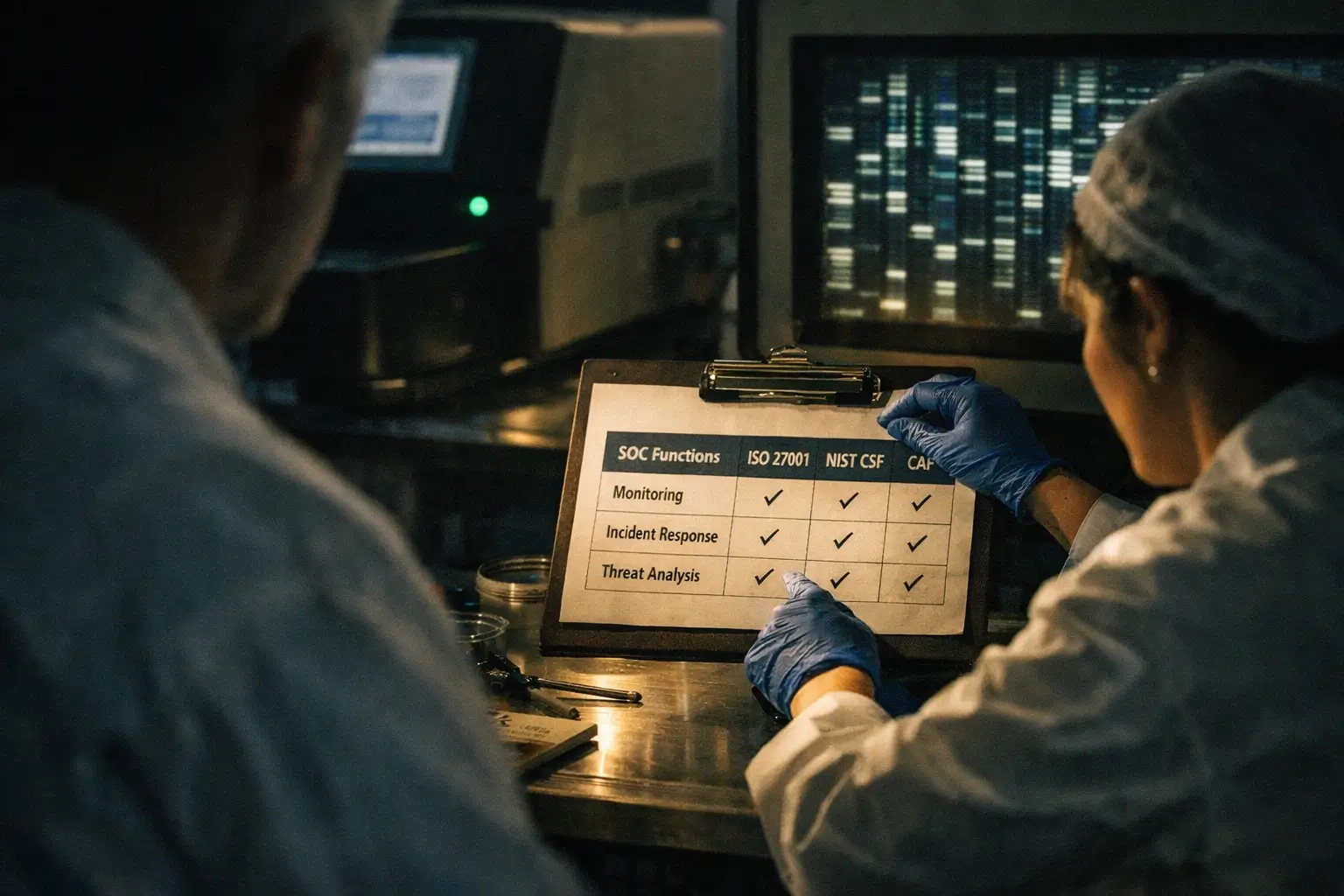
When building or improving a SOC cyber security capability, it helps to see how a SOC aligns with recognised frameworks and compliance standards. At CyPro, we map SOC operations to global best practice so your investment strengthens both your security posture and regulatory compliance.
Here’s a quick overview of how SOC functions connect to common frameworks:
- ISO 27001: Supports clauses on Information Security Incident Management (Annex A.16) and Monitoring and Logging (A.12.4), ensuring incidents are detected, analysed and resolved efficiently.
- NIST CSF: Directly links to Detect and Respond functions, providing the capability to identify anomalies and act on them swiftly.
- Cyber Assessment Framework (CAF): Ties into principles B2 and C2 around continuous monitoring and effective response to cyber events.
- GDPR: Helps demonstrate accountability and timely breach detection, supporting Articles 32 and 33 on security and notification.
- PCI-DSS: Aligns with requirements for logging, monitoring and incident response to protect cardholder data.
- SOC 2 Compliance: Reinforces Trust Services Criteria for security and confidentiality, helping prove robust data protection practices.
Our team integrates these frameworks into every SOC design, whether it’s built in-house or delivered through our SOC as a Service model. By embedding compliance into daily monitoring and response, we make sure your SOC cyber security capability supports regulatory goals and builds client trust.
✅ What Organisations Should Do

Building or improving your SOC cyber security capability starts with taking practical, measurable steps. It’s not about overnight transformation – it’s about steady progress that strengthens your organisation’s defences and resilience over time. Here’s what we recommend to get started:
- Assess your current maturity: Review how your SOC operates today. Map out detection coverage, response speed and reporting quality to identify clear gaps.
- Lock down access controls: Enable multifactor authentication across all accounts, prioritising admin and remote access. Limit privileges to what’s necessary.
- Remove legacy systems: Inventory old or unused servers, applications and devices. Decommission or patch anything not actively supported.
- Improve monitoring and detection: Enhance logging visibility across your network, endpoints and cloud. If in-house coverage is limited, our SOC as a Service or Managed Detection & Response (MDR) can provide round-the-clock support.
- Define governance: Set clear roles and responsibilities for your SOC team. Include credential lifecycle management and escalation workflows.
- Test your response plan: Run tabletop exercises regularly. Simulate incidents like ransomware or data leaks to test reaction speed and recovery preparedness.
- Validate your readiness: Schedule external audits, penetration tests or a SOC 2 Compliance assessment to benchmark your progress.
We supported a regional healthcare provider struggling with slow incident response and inconsistent monitoring across its IT environment. Working with our Senior SOC Engineers, we introduced improved log correlation and automated detection rules using our Managed Detection & Response service.
Within six months, false positives dropped by 40% and mean time to detect incidents fell from 18 hours to under three. The organisation also passed its annual compliance audit without findings, giving leadership confidence in its upgraded SOC cyber security posture.
🔚 Wrapping Up Your SOC in Cyber Security Strategy
Building a strong SOC cyber security capability is one of the smartest moves an organisation can make. It’s not just about technology – it’s about people, processes and proactive defence. A well-run SOC helps you spot risks early, meet compliance standards and make better decisions based on real-time insight.
A SOC turns cyber security from reactionary to proactive. With continuous monitoring, expert analysis and clear response plans, your business gains confidence, compliance and control over its security posture.
At CyPro, we combine services like SOC as a Service and Managed Detection & Response (MDR) to help organisations stay secure without the overhead of running a full in-house operation. Whether you’re reviewing your current setup or building from scratch, we can help align your security operations with your wider goals through our Cyber Strategy & Roadmap.
If your business is ready to strengthen its SOC cyber security posture, now’s the time to act. Review your current defences, prioritise what matters most and reach out to us to discuss how we can support your next steps. You’ll move from reacting to threats to confidently preventing them.











