Table of Contents
🔍 Understanding SOC Meaning: Why It Matters

When people talk about cyber defence, the term “SOC” often comes up, but what exactly does it mean? In simple terms, SOC meaning refers to a Security Operations Centre, a dedicated function responsible for detecting and responding to cyber attacks. According to the NCSC, most SOCs focus on monitoring and reacting to threats, though their scope can vary widely depending on the organisation’s needs.
At CyPro, we know many teams struggle to understand how a SOC fits into their wider cyber security strategy. Whether managed internally or through services like our SOC as a Service or Managed Detection & Response (MDR), an effective SOC helps minimise risk and keep operations running smoothly.
In this guide, we’ll break down SOC meaning in practical terms. You’ll learn what a SOC does, why it’s important, and how it evolves as organisations mature. By the end, you’ll have a clear picture of how this capability strengthens your cyber resilience and what steps to take if you’re considering building or improving your own SOC.
📖 What This Capability Is
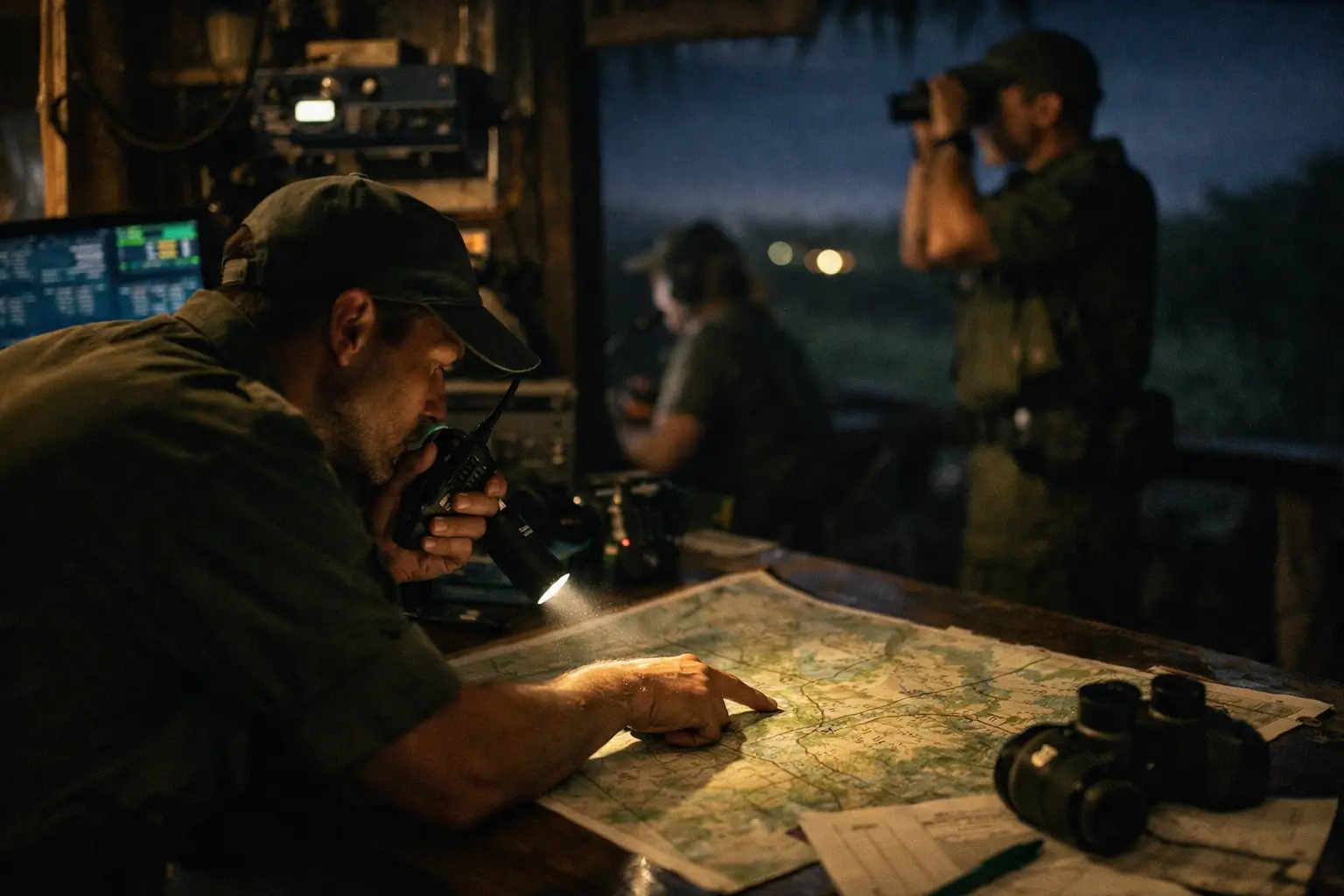
When we talk about soc meaning, we’re really talking about a team and a process that keeps watch over an organisation’s digital world. A Security Operations Centre is like a 24/7 command room for cyber defence, somewhere skilled analysts and smart tools work together to spot suspicious activity, investigate alerts and respond before minor issues become major problems. Think of it as the digital equivalent of a neighbourhood watch, always scanning for anything unusual and ready to act fast when needed.
The core purpose of a SOC is simple: visibility and response. By continuously monitoring networks, systems and data, it enables organisations to identify threats early and limit damage when attacks occur. This constant vigilance means issues can be contained quickly, reducing downtime and protecting both reputation and revenue.
At CyPro, we see the SOC as the centrepiece of an organisation’s wider cyber strategy. It connects detection, response and prevention, linking IT teams, management and business operations. Whether built in-house or supported through services like our SOC as a Service or Managed Detection & Response (MDR), the goal remains the same: understanding what’s happening across your environment so you can act with confidence.
In short, understanding soc meaning is about recognising that security isn’t static. A SOC enables continuous improvement, helping organisations stay ahead of attackers and maintain resilience in an ever-changing digital world.
A SOC provides continuous monitoring, rapid response and peace of mind. It’s the hub that keeps your organisation’s cyber defence alert and effective.
⚡ Why SOC Meaning Matters

Understanding soc meaning goes beyond knowing what the acronym stands for. A Security Operations Centre directly impacts how well an organisation can protect its data, meet compliance obligations and maintain customer trust. For decision-makers, the value lies in turning reactive defence into proactive risk management, something every business now needs as attacks become more sophisticated and regulators tighten expectations around breach response and reporting.
For most organisations, a SOC delivers clear business benefits:
- Risk reduction – Continuous monitoring helps identify and contain threats before they disrupt operations.
- Regulatory confidence – Having a SOC supports compliance with frameworks such as ISO 27001 and helps demonstrate due diligence to auditors and customers.
- Cost control – Early detection avoids expensive downtime and recovery costs.
- Reputation protection – Rapid response limits damage to brand and customer relationships.
At CyPro, we often see businesses gain stronger resilience through our SOC as a Service and Managed Detection & Response (MDR) solutions, which provide 24/7 oversight without the overhead of building a full in-house team.
We worked with a mid-sized financial services firm that faced repeated phishing and malware attempts targeting its client portal. Their internal IT team was stretched thin, reacting to incidents after they occurred.
By implementing our SOC as a Service and automated threat detection tools, we reduced false positives by 60% and improved incident response times from hours to minutes. Within three months, the firm saw a measurable drop in successful attacks and gained confidence in meeting regulatory reporting obligations.
The result was a safer environment and renewed trust from customers and auditors alike.
Knowing soc meaning isn’t just technical, it’s about understanding how a SOC protects your business, reduces risk and supports compliance in today’s fast-moving digital world.
🧩 Key Components of a SOC

When exploring soc meaning in depth, it helps to break down what actually makes up a Security Operations Centre. A SOC isn’t just a team or a piece of software, it’s a combination of processes, controls, technology and people working together to keep an organisation secure. Each component plays a key role in maintaining visibility, detecting threats and responding effectively.
Processes
Clear, repeatable processes form the backbone of every SOC. They ensure consistency and speed when incidents occur.
- Incident detection and response: Defined workflows for identifying, assessing and resolving threats.
- Threat analysis: Structured investigation practices for understanding attacker behaviour and intent.
- Asset inventory management: Maintaining visibility of all devices and systems under protection.
- Compliance monitoring: Ensuring operations align with regulations such as GDPR and CCPA.
- Escalation procedures: Clear handoff between analysts, responders and management when serious threats arise.
Controls
Controls are what enforce the SOC’s processes, they provide assurance that the right checks and protections are in place.
- Access controls: Restrict who can view and modify sensitive data or systems.
- Detection rules: Automated logic within monitoring tools to spot unusual behaviour.
- Data retention policies: Manage how logs and alerts are stored for investigation and compliance.
- Response controls: Pre-defined containment actions such as isolating infected endpoints or disabling compromised accounts.
Tools and Technology
Technology underpins everything a SOC does. It gathers data, triggers alerts and supports the team’s decision-making.
- SIEM platforms: Aggregate and analyse logs from across the environment.
- Endpoint detection tools: Identify suspicious activity on user devices.
- Threat intelligence feeds: Provide external insights into current attack trends.
- Automation and orchestration: Speed up response times and reduce manual effort.
- Reporting dashboards: Summarise activity for management and compliance reviews.
At CyPro, we often integrate these technologies through our SOC as a Service and Managed Detection & Response (MDR) offerings, giving organisations access to advanced tools without the complexity of managing them in-house.
Roles and Responsibilities
People are the most important part of the SOC. Technology alone can’t interpret context or make risk-based decisions.
- Analysts: Monitor alerts, perform triage and escalate issues when needed.
- Incident responders: Lead containment and remediation efforts during active threats.
- Threat hunters: Look for hidden or emerging risks that automated systems might miss.
- SOC managers: Oversee operations, reporting and resource planning.
- Compliance specialists: Ensure procedures align with data protection and regulatory standards.
Understanding soc meaning means recognising that a SOC thrives on four pillars: defined processes, strong controls, smart technology and skilled people, all working together to keep your organisation safe and compliant.
📊 Maturity Levels: What Good Looks Like

When exploring soc meaning, it’s useful to understand that not all Security Operations Centres operate at the same maturity level. SOCs evolve over time, moving from ad hoc monitoring to fully optimised operations. This journey reflects how well a team integrates people, processes and technology to manage cyber threats effectively.
Below is a simple view of typical SOC maturity stages. It can help you assess where your organisation sits today and what steps might improve your capability.
| Maturity Stage | Key Traits | Indicators of Strength |
|---|---|---|
| Ad Hoc | Reactive and informal. Limited monitoring, often reliant on manual checks. | Few or no documented processes. Incidents addressed only after impact. |
| Defined | Processes outlined and basic tools in use. Responsibility for detection and response is clear. | Some automation and reporting. Still gaps in visibility and coordination. |
| Managed | Consistent monitoring supported by trained analysts. Metrics used to measure performance. | Incident response is repeatable and auditable. Integration with wider IT operations. |
| Optimised | Continuous improvement driven by intelligence and automation. Hybrid or co-managed models often used, as seen in Microsoft’s guidance. | High visibility, proactive threat hunting and strong alignment with business goals. |
At CyPro, we often help organisations progress from defined to managed stages through services such as our SOC as a Service and Managed Detection & Response (MDR). These approaches bring consistent monitoring, expert analysis and scalable processes without the overhead of building everything in-house. For those already operating at a managed level, our Security Assessments & Audits can highlight opportunities to optimise further.
Understanding soc meaning in the context of maturity helps leaders recognise that a SOC isn’t static. It’s a capability that grows with experience, investment and collaboration.
What good looks like is a SOC that’s proactive, well-integrated and continuously improving. It combines skilled people, clear processes and smart tech to deliver confident, ongoing protection.
⚠️ Common Mistakes to Avoid When Understanding SOC Meaning

When exploring soc meaning and what a Security Operations Centre actually does, many organisations stumble over a few recurring pitfalls. These slip-ups can slow down progress, waste investment, or leave gaps in defence. Here are the most common mistakes we see and how to sidestep them.
- Starting without clear objectives – Some teams rush into building a SOC without knowing what success looks like. This happens when the focus is on tools rather than outcomes. Without defined goals, a SOC can become a noisy alert hub instead of a strategic defence centre. To avoid this, establish measurable aims from day one – things like reducing detection time or improving incident response.
- Underestimating the true cost – The expense of 24/7 monitoring, tooling and skilled analysts often catches organisations off guard. A SOC requires continuous investment, not just setup funds. We often advise exploring managed options like our SOC as a Service to balance capability and cost effectively.
- Technology misalignment – Buying multiple monitoring tools doesn’t guarantee effective defence. Integration matters. Many SOCs fail because systems don’t talk to each other, leaving blind spots. Our Managed Detection & Response (MDR) service helps unify monitoring and response under one coordinated approach.
Understanding soc meaning isn’t just about technology, it’s about clarity, integration and continuous improvement. Getting these basics right helps your SOC deliver genuine value and consistent protection.
🗺️ Framework Mapping: How SOC Meaning Connects to Standards

Understanding soc meaning isn’t just helpful for building your defence, it’s also key for aligning with recognised security frameworks. A well-structured SOC supports compliance across multiple standards by providing visibility, incident management and continuous improvement. At CyPro, we often help clients map their SOC functions to frameworks like ISO 27001, NIST CSF and the CAF to show how monitoring and response fit into broader governance efforts.
Here’s how a SOC typically connects to popular frameworks:
- ISO 27001: Clauses 6 (Planning), 8 (Operational Planning and Control) and Annex A.12 (Operations Security) relate directly to SOC processes around monitoring, logging and incident management.
- NIST CSF: Supports all five functions – Identify, Protect, Detect, Respond and Recover. The SOC primarily strengthens Detect and Respond.
- CAF: Aligns with principles like Protecting against cyber attacks and Responding to incidents.
- GDPR / PCI-DSS: SOC activities underpin requirements for data protection, breach detection and timely reporting.
In practice, mapping soc meaning to these frameworks helps organisations demonstrate compliance and improve maturity. Whether using our SOC as a Service or Managed Detection & Response (MDR), we ensure SOC capabilities are built around recognised best practice, making audits smoother and oversight stronger.
✅ What Organisations Should Do Next

Understanding soc meaning is one thing; putting it into practice is another. To build or strengthen your Security Operations Centre, focus on practical steps that improve visibility, response and resilience. Here’s what we recommend:
- Review access controls – Enable MFA across all accounts, especially remote and admin access. Regularly audit permissions and revoke unused credentials.
- Inventory and decommission legacy systems – Identify old or unused assets, remove them safely and maintain a strong patch management process to reduce exposure.
- Enhance monitoring and detection – Improve logging and alerting across your IT environment. Consider leveraging services like our SOC as a Service or Managed Detection & Response (MDR) for continuous oversight.
- Define governance – Clarify roles, responsibilities and credentials lifecycle. Everyone should know who owns each stage of an incident response.
- Test your response plans – Run tabletop exercises to simulate real attacks and ensure your team knows how to act. Keep backup and recovery plans up to date.
- Seek external assurance – Commission independent audits, penetration tests or a security maturity assessment to validate your SOC’s effectiveness.
We worked with a UK-based manufacturing business that had basic logging but limited visibility into unusual network activity. Their SOC analysts often missed early indicators of compromise.
We helped them review access controls, deploy enhanced monitoring and run structured incident-response exercises. Within six months, detection accuracy increased by 45%, and mean response time dropped from two hours to less than 20 minutes.
The team gained confidence in handling incidents and used the findings to refine governance and patch management processes. These measurable improvements turned their SOC into a proactive defence capability rather than a reactive one.
To put soc meaning into action, start with strong access control, modern monitoring and clear governance. Regular testing and external validation help ensure your SOC evolves with your business and keeps threats in check.
✅ Wrapping Up: Understanding SOC Meaning

By now, the meaning of SOC should feel much clearer. A SOC isn’t just technology or a team of analysts, it’s an ongoing commitment to staying ahead of threats and maintaining trust. Building or improving this capability takes effort, but the payoff is lasting resilience, smoother operations and stronger confidence across the business.
Understanding soc meaning means recognising that a Security Operations Centre is both a mindset and a capability. It’s about continuous improvement, proactive defence and smart investment in people and technology.
At CyPro, we help organisations strengthen their security posture through services like our SOC as a Service and Managed Detection & Response (MDR). If you’re reviewing your current setup or considering where to begin, now’s a great time to take stock. Reach out to us to explore how we can support your next steps and help you turn your SOC vision into reality.










